New Facebook Login Scam Uses Sneaky Browser-in-Browser Trick

▼ Summary
– Hackers are increasingly using the browser-in-the-browser (BitB) phishing technique, developed in 2022, to steal Facebook credentials.
– The attack uses a fake browser pop-up within an iframe that mimics a legitimate login page, making the deception visually convincing.
– Recent campaigns impersonate legal or security notifications and use shortened URLs and fake CAPTCHAs to appear more legitimate.
– Attackers also host phishing pages on trusted cloud platforms like Netlify and Vercel to bypass security filters and gain user trust.
– Protection advice includes manually navigating to official sites, checking if pop-ups can move outside the browser window, and enabling two-factor authentication.
A sophisticated new phishing campaign is targeting Facebook users with a deceptive method known as the browser-in-the-browser (BitB) technique. This scam creates a convincing illusion of a legitimate login window directly within a victim’s web browser, making it exceptionally difficult to distinguish from a real authentication prompt. Over the past six months, threat actors have increasingly adopted this approach to steal credentials, which they then use to spread further scams, harvest sensitive personal data, or commit identity fraud. With billions of active accounts, Facebook remains a top target for these malicious operations.
The core of the attack involves luring users to a webpage controlled by the hackers. Once there, they are presented with a fake browser pop-up that contains a login form. This pop-up is not a separate window from the operating system, but rather a cleverly crafted iframe, a webpage element, designed to mimic the exact look of a Facebook or Meta login portal. Cybercriminals can customize this fake window with a deceptive title and URL bar, enhancing the illusion and tricking even vigilant users.
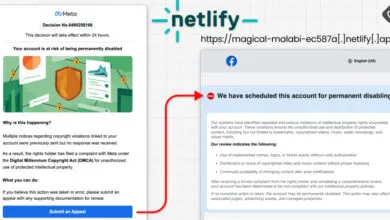
Recent phishing emails fueling these attacks have impersonated official-sounding entities. Common lures include fake legal notices from law firms alleging copyright infringement, threats of imminent account suspension, or urgent security alerts from Meta warning of unauthorized login attempts. To bolster their credibility and evade security filters, attackers often use shortened URLs and even incorporate fake CAPTCHA pages that appear to be from Meta.
In a parallel development, security researchers have noted a surge in phishing pages hosted on legitimate, trusted cloud platforms such as Netlify and Vercel. These pages impersonate Meta’s official Privacy Center, only to redirect visitors to fraudulent appeal forms that harvest personal information. This abuse of reputable infrastructure helps malicious pages bypass traditional security checks and lends them an unwarranted air of legitimacy.
The adoption of the BitB method marks a significant escalation from standard phishing campaigns. By exploiting user familiarity with standard login pop-ups, this technique makes visual detection of the fraud nearly impossible, as the fake window is rendered seamlessly within the browser environment. The malicious iframe is tethered to the underlying browser tab and cannot be dragged outside of it, which is a key detail that can reveal the scam.
To protect yourself from these advanced threats, adopt a cautious and proactive approach. If you receive any email or message about account security or violations, never click on the links or buttons within it. Instead, manually type the official website address, like facebook.com, into a new browser tab and check your account notifications directly. When any pop-up asks for your login details, try to drag the window. If it cannot be moved outside the main browser window, it is almost certainly a malicious iframe.
Enabling two-factor authentication (2FA) on your account is one of the most effective defensive steps you can take. While not a perfect solution, it creates a critical additional security barrier. Even if your password is stolen, the attacker would still need that second factor, like a code from your phone, to gain access, significantly reducing the risk of a successful account takeover.
(Source: Bleeping Computer)