Urgent Patch for Critical Cisco SD-WAN Zero-Day Flaw
▼ Summary
– A critical zero-day authentication bypass vulnerability (CVE-2026-20127) in Cisco SD-WAN products is being actively exploited, allowing attackers to gain administrative privileges.
– Multiple Five Eyes security agencies have issued an urgent directive for customers to immediately patch both this new flaw and a related legacy vulnerability (CVE-2022-20775).
– The US CISA has mandated all federal agencies to find and patch these vulnerabilities by a specific deadline in February 2026.
– Attackers are compromising SD-WAN systems to add malicious rogue peers, enabling them to gain root access and maintain persistent control of the network.
– Affected organizations are advised to follow a detailed hardening guide that includes steps for network perimeter controls, access security, and logging.
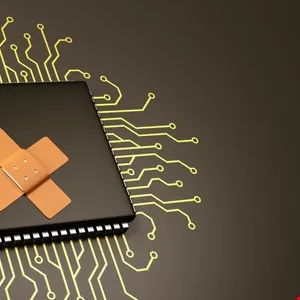
A critical security flaw in widely used Cisco networking equipment demands immediate attention from organizations worldwide. Government cybersecurity agencies across the UK, US, Canada, Australia, and New Zealand have issued a joint alert, urging administrators to apply a patch for a severe zero-day vulnerability that attackers have actively exploited. This flaw, identified as CVE-2026-20127, carries the highest possible severity rating with a CVSS score of 10.0, indicating the potential for catastrophic damage if left unaddressed.
The vulnerability resides within the peering authentication mechanism of both Cisco Catalyst SD-WAN Controller and Cisco Catalyst SD-WAN Manager. Cisco’s advisory explains that this defect allows an unauthenticated remote attacker to bypass standard security checks entirely. By sending specially crafted requests to a vulnerable system, an adversary could gain administrative privileges. Once inside, they could log in using a high-privileged internal account, access the NETCONF protocol, and manipulate the entire SD-WAN fabric’s configuration, giving them extensive control over network traffic and security policies.
Investigations by international security partners reveal a sophisticated and calculated attack pattern. Threat actors are not just exploiting this new flaw in isolation. Forensic analysis indicates they first downgrade a target system to an older software version to leverage a separate, known privilege escalation bug tracked as CVE-2022-20775. After using that legacy vulnerability to elevate their access, they then restore the system to its original version, ultimately achieving full root-level control. This multi-stage approach demonstrates a high level of planning and underscores the critical need to patch both the new zero-day and the older 2022 vulnerability.
The urgency of the situation is reflected in official mandates. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has taken the rare step of issuing an emergency directive, compelling all federal agencies to locate and remediate these vulnerabilities by a strict deadline. CISA’s acting director emphasized that the ease of exploitation leaves no room for delay, a warning that private sector organizations should heed with equal seriousness. The directive serves as a stark reminder that these flaws present a clear and present danger to network integrity.
For organizations using the affected Cisco SD-WAN products, which are designed to secure connections between offices, data centers, and cloud services, specific hardening actions are required. The UK’s National Cyber Security Centre (NCSC) provided a detailed guide, noting that attackers are actively compromising systems to add malicious rogue peers. This stealthy technique allows them to establish a persistent foothold within the network infrastructure, enabling a wide range of follow-on malicious activities. The recommended steps are comprehensive, focusing on tightening network perimeter controls, restricting access to the SD-WAN manager, securing both the control and data planes, and implementing robust session timeout and logging policies. Taking these measures is not merely a recommendation but a necessary defense against an ongoing and sophisticated threat campaign.
(Source: Info Security)