Severe Linux threat catches world off guard

▼ Summary
– Publicly released exploit code for the Linux vulnerability CVE-2026-31431 (CopyFail) gives root access to virtually all Linux releases, alarming defenders in data centers and on personal devices.
– The exploit was released by Theori researchers five weeks after private disclosure to the Linux kernel team, which patched the flaw in specific kernel versions, but few distributions had incorporated the fixes.
– CopyFail is a local privilege escalation vulnerability that allows unprivileged users to become root, and a single exploit script works across all vulnerable distributions with no modification.
– The exploit enables attackers to hack multi-tenant systems, break out of Kubernetes containers, and inject malicious code into CI/CD workflows.
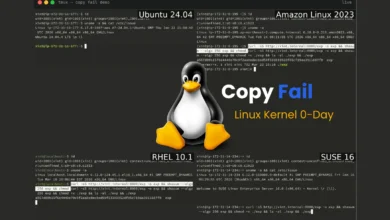
– The same Python exploit script reliably works on Ubuntu 22.04, Amazon Linux 2023, SUSE 15.6, and Debian 12, according to researcher Jorijn Schrijvershof.
A newly disclosed exploit targeting a critical Linux vulnerability has sent alarm through the cybersecurity community, as the flaw grants root access to nearly all major Linux distributions and remains largely unpatched across production environments and personal devices alike.
The vulnerability, designated CVE-2026-31431 and dubbed CopyFail, is a local privilege escalation bug that allows any unprivileged user to gain full administrative control over a system. Security firm Theori released both the vulnerability details and a working exploit on Wednesday evening, just five weeks after privately disclosing the issue to the Linux kernel security team. While the kernel team has released patches for versions including 7.0, 6.19.12, 6.18.12, 6.12.85, 6.6.137, 6.1.170, 5.15.204, and 5.10.254, most Linux distributions had not yet integrated those fixes by the time the exploit went public.
What makes CopyFail particularly dangerous is that the same single Python script works across all vulnerable distributions without any modifications. This means attackers can target Ubuntu 22.04, Amazon Linux 2023, SUSE 15.6, and Debian 12 with equal effectiveness, as confirmed by researcher Jorijn Schrijvershof in a detailed analysis published Thursday.
“‘Local privilege escalation’ sounds dry, so let me unpack it,” Schrijvershof wrote. “It means: an attacker who already has some way to run code on the machine, even as the most boring unprivileged user, can promote themselves to root. From there they can read every file, install backdoors, watch every process, and pivot to other systems.”
The implications extend far beyond single-machine compromises. With root access, an attacker can hack multi-tenant systems, break out of Kubernetes containers or other containerized environments, and inject malicious code into CI/CD pipelines through crafted pull requests. For data centers and cloud infrastructure, this represents a nightmare scenario where a single foothold can cascade into widespread compromise across entire clusters.
System administrators and security teams are now racing to apply patches, but the window of exposure is wide. The exploit code is publicly available, and the attack requires no specialized knowledge to execute. Organizations running Linux in any capacity should prioritize patching immediately, particularly for internet-facing systems and container orchestration platforms.
(Source: Ars Technica)