Linux Kernel 0-Day Flaw Affects All Major Distros Since 2017
▼ Summary
– A critical zero-day vulnerability (CVE-2026-31431) in the Linux kernel, introduced in 2017, allows any unprivileged local user to gain root access on all major Linux distributions.
– The flaw, named “Copy Fail,” is a logic bug in the authencesn cryptographic template, exploitable via the AF_ALG socket and splice() system call without requiring race conditions or compiled payloads.
– A 732-byte Python script achieves deterministic root access by performing a controlled 4-byte write into a page cache page of a readable file, corrupting its in-memory version without altering the on-disk file.
– The vulnerability functions as a Kubernetes container escape because the shared page cache allows a compromised container to corrupt setuid binaries visible to other containers and the host.
– The official fix reverts algif_aead.c to out-of-place AEAD operation, separating the TX and RX scatterlists; immediate mitigation includes disabling the algif_aead kernel module until the patch is applied.
A critical Linux kernel zero-day vulnerability has been publicly disclosed, giving any unprivileged local user the ability to gain root access on nearly every major Linux distribution shipped since 2017. Tracked as CVE-2026-31431 and nicknamed “Copy Fail,” this flaw was discovered by Theori researcher Taeyang Lee and later developed into a full exploit chain by the Xint Code Research Team using AI-assisted analysis.
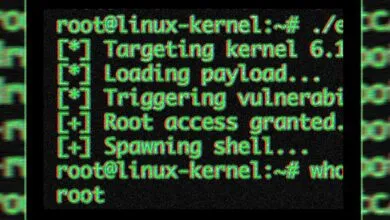
Copy Fail is a straight-line logic bug, not a race condition, residing in the kernel’s authencesn cryptographic template. It is reachable through the AF_ALG socket interface combined with the splice() system call. Unlike previous vulnerabilities like Dirty Cow (CVE-2016-5195) or Dirty Pipe (CVE-2022-0847), this one requires no race-winning, no kernel version offsets, no recompilation, and no compiled payloads.
A single 732-byte Python script using only standard library modules achieves deterministic root on every tested distribution and architecture. The exploit targets the kernel’s page cache, the in-memory representation of files, by triggering a controlled 4-byte write into a page cache page belonging to any file readable by the attacker.
Because the Linux kernel never marks the corrupted page as dirty for writeback, the on-disk file remains untouched. Standard checksum-based file integrity tools miss the modification entirely. The attacker then executes the corrupted in-memory version of a setuid binary such as `/usr/bin/su`, achieving root shell execution.
The vulnerability originates from a 2017 in-place optimization introduced to `algifaead.c` (commit `72548b093ee3`). When a user splices a file into a pipe and feeds it into an AFALG socket, the AEAD input scatterlist holds direct references to the kernel’s physical page cache pages of that file, not copies. For AEAD decryption operations, `algif_aead.c` set `req->src = req->dst`, making both source and destination point to the same combined scatterlist. This placed page cache pages into a writable destination scatterlist. The authencesn algorithm, used by IPsec for 64-bit Extended Sequence Number (ESN) support, then uses the caller’s destination buffer as scratch space to rearrange ESN bytes, writing 4 bytes at offset `assoclen + cryptlen` past the declared output boundary, directly into chained page cache pages.
Three independent, reasonable code changes across 2011, 2015, and 2017 converged to create this exploitable condition, with nobody connecting their intersection for nearly a decade.
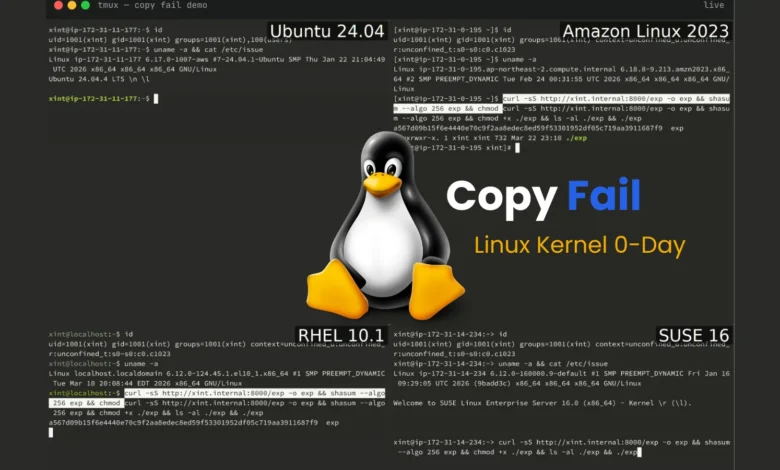
The same unmodified exploit script achieved root shell on all four tested platforms:
- Ubuntu 24.04 LTS (kernel 6.17.0-1007-aws)The vulnerability was introduced with kernel 4.14 and affects all distributions through the unfixed line. Beyond local privilege escalation, Copy Fail functions as a Kubernetes container escape primitive. Because the page cache is shared across all processes on a host, including across container boundaries, a compromised container can corrupt setuid binaries visible to other containers and the host kernel. Part 2 of the Xint Code research series covers full Kubernetes node compromise.The official fix (commit `a664bf3d603d`) reverts `algifaead.c` to out-of-place AEAD operation, permanently separating the TX scatterlist (which may contain page cache pages) from the RX scatterlist (the user’s output buffer). This eliminates the `sgchain()` mechanism that linked page cache pages into the writable destination.Immediate mitigations pending kernel update include applying the upstream kernel patch via your distribution’s update channel and disabling the `algif_aead` kernel module to eliminate the attack surface:“` echo “install algif_aead /bin/false” > /etc/modprobe.d/disable-algif-aead.conf rmmod algif_aead 2>/dev/null “`The vulnerability was reported to the Linux kernel security team on March 23, 2026, with patches committed to mainline on April 1, 2026, CVE assigned on April 22, 2026, and public disclosure on April 29, 2026. System administrators are urged to apply kernel updates immediately.