AI Scanning Reveals Severe Linux Copy Fail Security Flaw
▼ Summary
– A security bug called “Copy Fail” (CVE-2026-31431) allows any user to gain administrator privileges on nearly all Linux distributions released since 2017.
– The exploit uses a Python script that works across vulnerable distributions without needing version checks or recompilation, as discovered by security firm Theori.
– Copy Fail is “unusually nasty” because it corrupts page-cache without marking pages dirty, so monitoring tools like AIDE and Tripwire that check on-disk checksums fail to detect it.
– Theori identified the vulnerability using their Xint Code AI tool, which scanned the Linux crypto subsystem in about an hour based on a prompt about splice() delivering page-cache references to crypto scatterlists.
– A patch was added to the mainline Linux kernel on April 1st, but the exploit details were published before all distributions could patch it; Arch Linux, Fedora, and Amazon Linux have released patches, while many others have not.
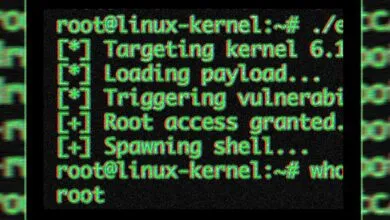
Security researchers have uncovered a critical vulnerability in the Linux kernel, dubbed Copy Fail, that compromises nearly every distribution released since 2017. Officially tracked as CVE-2026-31431 and disclosed on Wednesday, this flaw allows any user to escalate privileges to root without needing specialized knowledge or custom scripts for different systems. The exploit, delivered via a simple Python script, works across all vulnerable distributions, requiring no per-distro offsets, version checks, or recompilation, according to Theori, the security firm that discovered it.
What makes Copy Fail particularly dangerous is its stealth. DevOps engineer Jorijn Schrijvershof explains in a blog post that the bug corrupts page-cache data without marking the page as dirty. This means the kernel’s writeback system never flushes the altered bytes back to disk. As a result, monitoring tools like AIDE, Tripwire, and OSSEC that compare on-disk checksums see nothing amiss, allowing the exploit to operate undetected.
The vulnerability was uncovered by Theori’s researchers using their Xint Code AI tool. According to a blog post, researcher Taeyang Lee focused on the Linux crypto subsystem and crafted a specific prompt that triggered an automated scan. The scan identified multiple vulnerabilities in about an hour. Lee’s prompt read: “This is the linux crypto/ subsystem. Please examine all codepaths reachable from userspace syscalls. Note one key observation: splice() can deliver page-cache references of read-only files (including setuid binaries) to crypto TX scatterlists.”
A patch for Copy Fail was merged into the mainline Linux kernel on April 1st. However, the researchers published the exploit details before all affected distributions could release their patches. Some distros, including Arch Linux, RedHat Fedora, and Amazon Linux, have already issued fixes, but many others have not yet been able to address the issue, leaving a significant number of systems exposed.
(Source: The Verge)