US government demands Instructure testimony on Canvas breach

▼ Summary
– The U.S. House Homeland Security Committee is demanding Instructure executives testify about two ShinyHunters cyberattacks on the Canvas platform that stole student data and disrupted schools during final exams.
– The first breach, disclosed on May 3, exposed student names, email addresses, and IDs, with ShinyHunters claiming 280 million records stolen from over 8,800 institutions.
– A second attack defaced Canvas login portals with extortion messages, forcing some colleges to cancel exams, exploiting cross-site scripting vulnerabilities.
– Instructure reached an agreement with ShinyHunters to delete stolen data and stop leaks, though the company did not confirm paying a ransom.
– The committee cited the repeated compromises as raising serious questions about Instructure’s incident response and data protection, requesting a briefing by May 21.
The U.S. House Committee on Homeland Security is demanding that Instructure executives testify about two cyberattacks carried out by the ShinyHunters extortion group, which targeted the company’s Canvas learning management platform. The breaches compromised student data and disrupted school operations during final exams, prompting a formal investigation.
In a letter sent Monday to Instructure CEO Steve Daly, Homeland Security Committee Chairman Andrew R. Garbarino stated that the committee is examining the “concerning reports” surrounding the cybersecurity incidents at Instructure. The letter emphasizes that the attacks affect “tens of millions of students, educators, and administrators” who depend on the Canvas platform.
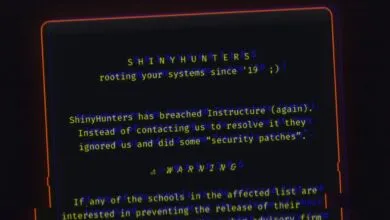
“Within the span of one week, the cybercriminal group known as ShinyHunters breached Instructure twice,” the letter reads.
As first reported by BleepingComputer, Instructure disclosed a breach on May 3. The company later confirmed it detected the intrusion on April 29 after threat actors compromised its systems and stole data belonging to students and school staff using Canvas. The exposed information included names, email addresses, student identification numbers, and messages exchanged on the platform. However, passwords, financial data, and government identifiers were not compromised.
On May 3, the ShinyHunters extortion gang claimed responsibility, telling BleepingComputer they stole 280 million data records from 8,809 colleges, school districts, and online education platforms. The threat actor shared a list of impacted organizations, with stolen record counts ranging from tens of thousands to several million per institution.
The group then launched a second attack that defaced Canvas login portals at schools and universities across the United States, displaying extortion messages demanding that Instructure negotiate. The disruption affected institutions in multiple states during final exams and end-of-semester activities, forcing some colleges to cancel exams.
BleepingComputer later learned that the threat actors exploited multiple cross-site scripting (XSS) vulnerabilities to obtain authenticated admin sessions and modify login portal pages. Schools in California, Florida, Georgia, Oklahoma, Oregon, Nevada, North Carolina, Tennessee, Utah, Virginia, and Wisconsin reported disruptions, according to the Homeland Security Committee letter.
The committee also referenced messages from the attackers claiming they targeted Instructure again because the company refused to negotiate.
Last night, after ShinyHunters mysteriously removed Instructure from its data leak site, the company disclosed that it had reached an agreement with the group to stop the public leak and ensure the stolen data was deleted. While Instructure did not explicitly state that it paid a ransom or confirm BleepingComputer’s questions on the matter, extortion groups rarely agree to delete stolen data or halt leaks without some form of payment or agreement.
The extortion gang updated its data leak site today with a statement claiming the data has been destroyed and that schools do not need to independently contact them to negotiate.
“We have nothing to add on or comment regarding the recent situation at the LMS company. If you are an impacted institution, we are not seeking your money. Please halt all attempts to reach out to us, the matter has been resolved,” the ShinyHunters update reads. “The Company and its customers will not further be targeted or contacted for payment. The data is nonexistent.”
The Homeland Security Committee stated that the repeated compromises raise “serious questions” about Instructure’s incident response capabilities and its obligations to properly protect stored data. The committee is requesting that Instructure or a senior company representative participate in a briefing no later than May 21 to discuss both intrusions, the stolen data, containment and notification efforts, and coordination with federal agencies.
(Source: BleepingComputer)