Windows 11 Recall Database Accessed by TotalRecall Tool
▼ Summary
– Microsoft launched Copilot+ PCs with NPUs to enable local AI features, aiming to improve security and privacy.
– The Recall feature initially stored unencrypted screenshots and user activity data, creating a major security vulnerability.
– Following criticism, Microsoft delayed Recall and added encryption, better sensitive data filtering, and made it opt-in by default.
– Despite improvements, security researchers argue Recall remains a privacy risk due to its extensive activity logging.
– An updated tool called “TotalRecall Reloaded” demonstrates ongoing potential vulnerabilities in the feature.
The launch of Microsoft’s Copilot+ PCs two years ago introduced a new class of hardware designed to leverage integrated neural processing units. These NPUs promised to unlock powerful local AI features, shifting processing away from the cloud and potentially improving both performance and user privacy. Among the initial flagship capabilities was Recall, a tool intended to act as a photographic memory for your computer by capturing screenshots of user activity.
However, the initial implementation of Recall created a significant security vulnerability. Instead of safeguarding the data, the feature stored all its screenshots and a comprehensive activity log in completely unencrypted files on the local drive. This design flaw meant that anyone with access to the machine, whether physically or remotely, could easily extract vast amounts of sensitive personal information spanning weeks or months of use.
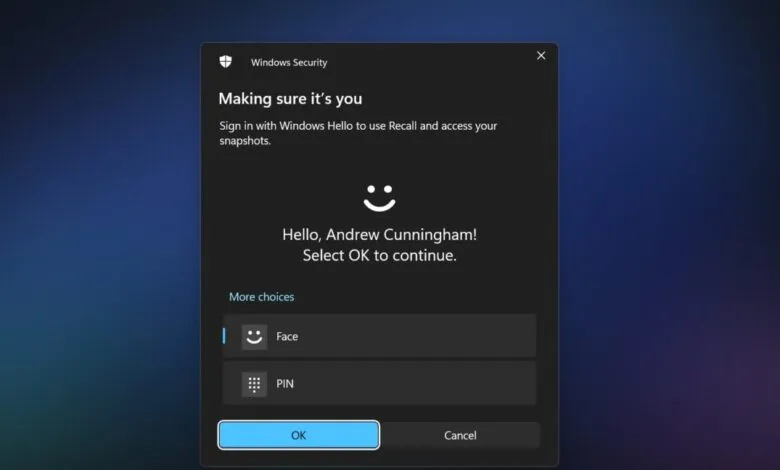
Following intense scrutiny from security researchers and journalists, Microsoft postponed the feature’s public release for nearly a year to conduct a major overhaul. The revised version of Recall now employs Windows Hello authentication as a mandatory gatekeeper, encrypts all locally stored data, and incorporates better filters to exclude sensitive content like financial details. Perhaps most critically, the feature is now disabled by default on compatible systems, requiring users to opt-in explicitly.
Despite these substantial improvements, the fundamental nature of a tool that continuously logs nearly all PC activity remains a persistent privacy risk. Security expert Alexander Hagenah, who originally developed the “TotalRecall” utility to demonstrate how easily the unsecured data could be extracted, has released an updated version. His new “TotalRecall Reloaded” tool aims to highlight what he views as ongoing potential vulnerabilities within the system’s current architecture.
(Source: Ars Technica)