WhatsApp Security Flaw Exposed 3.5 Billion Users
▼ Summary
– WhatsApp’s contact discovery feature allows users to find contacts by phone number but also enables mass extraction of user data through automated number checking.
– Austrian researchers extracted 3.5 billion WhatsApp users’ phone numbers and accessed profile photos for 57% and profile text for 29% of them using this method.
– Meta failed to implement rate-limiting on contact discovery requests despite a 2017 warning, allowing researchers to check around 100 million numbers per hour.
– The researchers described this as the largest exposure of phone numbers and user data ever documented, though they responsibly deleted the data after notifying Meta in April.
– Meta fixed the vulnerability by October with stricter rate-limiting, stating no evidence of malicious abuse was found and that private user messages remained secure due to end-to-end encryption.
A recent investigation has revealed a significant security vulnerability within WhatsApp’s contact discovery system, potentially impacting its global user base of 3.5 billion individuals. The platform’s straightforward method for adding new contacts, simply by entering a phone number, unintentionally enabled researchers to systematically verify the existence of nearly every WhatsApp account worldwide. This process also frequently exposed users’ profile names and photographs, creating an unprecedented data exposure incident.
By repeatedly checking phone numbers through WhatsApp’s web application, a team of Austrian academics managed to compile a list matching virtually every active user. For approximately 57% of these accounts, they could retrieve profile images, while status text was accessible for an additional 29%. Although a similar issue was flagged back in 2017, Meta, WhatsApp’s parent company, had not implemented sufficient safeguards to restrict the volume or speed of such automated queries. This oversight allowed the research team to validate around one hundred million numbers each hour.
The academics described the situation as what could have been the most extensive data breach ever recorded, had it not been part of a controlled and ethical research project. Aljosha Judmayer, a researcher from the University of Vienna involved in the study, emphasized that this represents the broadest known exposure of telephone numbers and associated personal details documented to date.
After notifying Meta through its bug bounty program in April, the researchers securely erased their collected dataset. By October, Meta addressed the vulnerability by enforcing stricter rate-limiting protocols designed to block bulk contact discovery attempts. Max Günther, another co-author of the study, pointed out that until this fix was applied, any malicious actor employing the same technique could have harvested the same trove of information with relative ease.
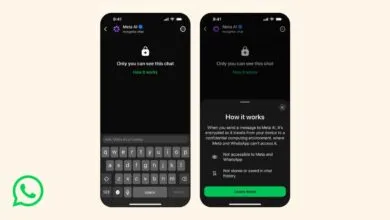
In an official statement, Meta expressed gratitude to the researchers for their responsible disclosure. Nitin Gupta, WhatsApp’s Vice President of Engineering, characterized the accessible data as “basic publicly available information,” noting that profile photos and statuses remained hidden for users who had adjusted their privacy settings accordingly. He affirmed that the company’s ongoing anti-scraping initiatives were validated and strengthened by the study’s findings. Gupta also reassured users that private messages remained protected by end-to-end encryption throughout, and no evidence suggests this method was exploited by malicious parties.
(Source: Wired)