All Related Articles for: The Hidden Vulnerabilities in Email Security
Found 11 articles related to this post based on shared entities and topics.
-
 December 3, 202517%
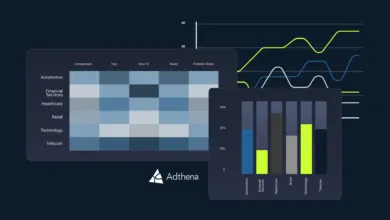
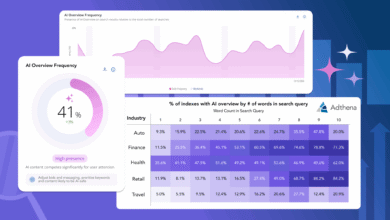
December 3, 202517%AI vs. Ads: The Fight for Ranking Supremacy
Google's AI Overviews are pushing paid and organic search…
Entity similarity: 29% | Topic similarity: 0%Read More » -
 February 26, 202617%
February 26, 202617%Google AI Overviews: The Real Impact on Paid Search
Google's AI Overviews in search results are reducing ad…
Entity similarity: 28% | Topic similarity: 0%Read More » -
 November 20, 202517%
November 20, 202517%Industries Adapting to Answer-Driven Search
The shift from traditional search results to AI-generated direct…
Entity similarity: 28% | Topic similarity: 0%Read More » -
 November 21, 202516%
November 21, 202516%Global Supply Chain Breaches Hit Nearly Every Company
Nearly all organizations (97%) now face negative impacts from…
Entity similarity: 27% | Topic similarity: 0%Read More » -
 November 12, 202516%
November 12, 202516%CISOs Speak the Language of Money to Secure Funding
CISOs are adopting financial language to frame cybersecurity as…
Entity similarity: 27% | Topic similarity: 0%Read More » -
 November 5, 202516%
November 5, 202516%Forescout eyeSentry: Continuous Cloud Exposure Management
Forescout launched eyeSentry, a cloud-native platform that helps enterprises…
Entity similarity: 27% | Topic similarity: 0%Read More » -
 November 4, 202516%
November 4, 202516%Google’s AI Overhauls Paid Search: What You Need to Know
Google's AI Overviews are reducing paid search click-through rates…
Entity similarity: 27% | Topic similarity: 0%Read More » -
 August 8, 202515%
August 8, 202515%Cybercriminals Target Personal Data – And It’s Paying Off
Cybercriminals are using advanced phishing kits like Evilginx and…
Entity similarity: 24% | Topic similarity: 0%Read More » -
 October 12, 202513%
October 12, 202513%Create Connected Data Ecosystems for AI at Scale
Modern integration platforms transform fragmented IT systems into streamlined…
Entity similarity: 22% | Topic similarity: 0%Read More » -
 April 17, 202612%
April 17, 202612%Bitdefender GravityZone Adds Email Threat Protection
The business email threat landscape is severe, with Business…
Entity similarity: 0% | Topic similarity: 30%Read More » -
 January 3, 202611%
January 3, 202611%Hospitals Overwhelmed by Unmanageable Threats
The healthcare sector faces a severe cybersecurity crisis, with…
Entity similarity: 14% | Topic similarity: 8%Read More »