Topic: Security Risks
-

Hush Security Launches to Replace Legacy Vaults with Secretless Access
Hush Security has raised $11 million in seed funding to advance its policy-driven, just-in-time access model for machine-to-machine communication, replacing traditional vaults and static secrets. The company's approach provides real-time visibility, posture analysis, and prevention, addressing th...
Read More » -

Hold Off on the Hype: The Viral Moltbot AI Agent
Moltbot is a novel open-source AI assistant that proactively initiates tasks and integrates with popular messaging apps, but its complex server-based setup limits its accessibility to average users. The tool's always-on nature and extensive system permissions create severe security vulnerabilitie...
Read More » -

The Hidden Dangers of Unmanaged Identities
Unmanaged identities, including both human and machine accounts outside formal oversight, create critical security vulnerabilities by expanding the attack surface and undermining compliance and operational stability. These identities pose distinct risks such as excessive administrator permissions...
Read More » -

Enterprise Data's Fate in the Age of Ubiquitous GenAI
Generative AI's rapid business integration is creating significant new security vulnerabilities, accelerating data exposure, and outpacing existing organizational policies and controls. The adoption of these tools has led to a massive increase in sensitive data shared with AI applications, with a...
Read More » -

The Hidden Danger of BYOD: Your Personal Device is the Weakest Link
A large majority of organizations globally use Bring Your Own Device policies, but only half formally authorize them, leading to significant security vulnerabilities in remote and hybrid work environments. Unsecured personal devices pose risks like data leakage, malware infections, and shadow IT,...
Read More » -

OpenID Foundation's Plan to Tame Dangerous AI Agents
The rapid adoption of AI agents introduces significant security vulnerabilities, as they can bypass traditional digital security barriers, necessitating new, open identity and access management standards to prevent unauthorized access to sensitive data and processes. AI agents, enabled by technol...
Read More » -

Who Else Has Access to Your Wearable's Heartbeat Data?
The proliferation of smartwatches and connected medical devices enables remote health monitoring and personalized care, but it also introduces significant security vulnerabilities due to the constant flow of sensitive data. Ambiguity in health data ownership and sharing practices raises privacy c...
Read More » -

MIT Study: AI Agents Are Fast, Loose, and Out of Control
A major study of 30 agentic AI systems reveals widespread and critical gaps in security, transparency, and user control, with most failing to disclose risks or safety protocols. The research highlights a severe lack of monitoring and control, noting that several prominent agents offer no document...
Read More » -

Open Source Moltbot Draws Users Despite AI Risks
Moltbot is a rapidly growing open-source personal AI assistant that integrates with popular messaging apps, but experts warn it carries significant security and operational risks. Its key feature is a proactive communication style, initiating contact with reminders and alerts, which has led to co...
Read More » -

Google Unveils Chrome's AI Security Safeguards
The rise of intelligent web agents introduces significant security risks, including data loss and financial threats, prompting Google to develop a multi-layered security framework for Chrome to keep these features safe and user-controlled. Google's security approach includes a User Alignment Crit...
Read More » -
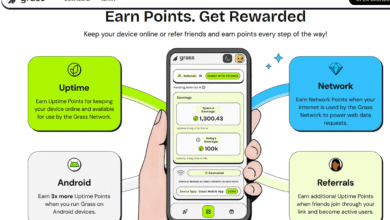
Your Android TV Box Could Be a Botnet
Popular Android TV streaming devices like Superbox secretly incorporate users' home networks into botnets, enabling cybercrime activities without their knowledge. These devices require users to install unofficial app stores and connect to suspicious services, such as Tencent QQ and Grass IO, whic...
Read More » -

Windows Recall: What It Is and Why You Should Enable It
Windows Recall is a new feature for Copilot+ PCs that captures periodic screenshots of user activity, enabling users to search through their digital history to find past documents, applications, or web pages. The feature utilizes Microsoft's Copilot AI to understand and intelligently search the c...
Read More » -

Scan Your MCP Security with Proximity's Open-Source Tool
Proximity is an open-source tool that scans Model Context Protocol (MCP) servers to catalog exposed prompts, tools, and resources, helping identify security vulnerabilities before deployment. It integrates with NOVA to detect threats like prompt injection and data exfiltration, allowing security ...
Read More » -

AI Agents on Your Team: The Unseen Security Risks
AI agents are evolving into autonomous systems that perform complex tasks like incident resolution and system management, introducing significant security challenges alongside efficiency gains. These autonomous agents differ from traditional tools by reasoning, adapting strategies, and accessing ...
Read More » -

AI's Speed Demands Faster Data Security Now
Generative AI is being rapidly adopted by businesses for innovation, but it introduces significant data security challenges, especially concerning data integrity and confidentiality. The reliance on high-quality data makes AI systems vulnerable to integrity-based threats, such as data tampering, ...
Read More » -

Bots Exposed: The Growing Threat of Data Leaks
Non-human identities (NHIs) like bots and automation scripts are now the fastest-growing security risk, leaking sensitive data more than human-related vulnerabilities. Machine identities outnumber human ones 144 to 1, with credentials often forgotten, overprivileged, or stored in risky locations ...
Read More » -

Google's Gmail Update Puts Millions of Accounts at Risk
Gmail is discontinuing POP3 email fetching and the Gmailify service, removing key protections for users who link older, third-party email accounts like Yahoo or Outlook. These changes will expose millions of users to unchecked spam and phishing, as Gmail's powerful AI-driven filters will no longe...
Read More » -

Protect Your Windows 10 From Hackers With This One Step
Windows 10's official security support ended in October 2025, leaving systems without critical patches and creating a significant, growing vulnerability risk. Users can temporarily mitigate this risk by enrolling in a paid Extended Security Updates program or by relying on Microsoft Defender upda...
Read More » -

Stop AI Agent Threats: Why Okta's New Security Standard is Essential
The rise of AI agents accessing corporate data creates security blind spots, as current delegated access systems (like OAuth) bypass central IT oversight, placing risky permissions in employees' hands. A new open standard, the Identity Assertion Authorization Grant (IAAG), proposes to give organi...
Read More » -

Perplexity's Computer: A Safer Alternative to OpenClaw?
Perplexity's Computer is a multiagent AI system that acts as a safer, controlled alternative to autonomous agents, using specialized models to reason, delegate, and execute tasks within a protected sandbox environment. It functions as a project manager, breaking down user requests into subtasks a...
Read More » -

Senior Devs Embrace 'AI Babysitter' Role for Vibe Coding's Payoff
Experienced developers are increasingly acting as "AI babysitters," spending significant time reviewing and correcting AI-generated code to fix errors and security flaws. The reliance on AI coding tools introduces risks like bypassing traditional review processes, creating new security vulnerabil...
Read More » -
Humans Are Infiltrating AI Bot Social Networks
Moltbook, a social platform for AI agents, is experiencing a unique inversion of authenticity problems, with humans impersonating bots to create viral content instead of the typical bot-impersonating-human issue. The platform's rapid growth and bizarre agent interactions were overshadowed by secu...
Read More » -

Clawdbot (Now Moltbot): Your Complete Guide to the Viral AI Assistant
Moltbot is a viral AI assistant that executes real-world tasks like managing calendars and booking flights, moving beyond simple conversation to proactive action. Its powerful ability to execute commands introduces significant security risks, including potential for malicious prompt injection att...
Read More » -

Google Admits Android Sideloading Is Now 'High Friction'
Google is developing a new, intentionally "high friction" process for installing apps outside the Play Store, featuring prominent security warnings but allowing knowledgeable users to bypass mandatory developer verification. The company frames this as an "Accountability Layer" to combat scams, ai...
Read More » -

Opera Neon AI Browser Launches: $20/Month for Power Users
Opera has launched its premium Neon AI browser for $19.90/month, targeting advanced users and competing directly with new AI-focused browsers and established players integrating AI. The browser provides unified access to multiple leading AI models and features four specialized agents for conversa...
Read More » -

Chrome Will Alert You Before Loading Unsafe Websites
Starting in October 2026, Google Chrome will automatically enable "Always Use Secure Connections" for all users, displaying bypassable warnings for unencrypted public websites to enhance security. The rollout will occur in phases, beginning with Enhanced Safe Browsing users in April 2026 and expa...
Read More » -
OS Agents Pose Rising Security Threat to Computers and Phones
AI-powered OS agents are rapidly evolving from research to commercial products, offering automation of complex tasks but introducing significant security risks that current systems may not handle. These agents excel at simple, repetitive tasks but struggle with context-dependent operations, while...
Read More » -

Microsoft tackles new security threats in Windows 11 AI tools
Microsoft is integrating advanced AI into Windows 11, introducing experimental agentic features that enable Copilot Actions to autonomously perform tasks like organizing files and scheduling appointments. These AI agents can make errors and pose novel security risks, prompting Microsoft to implem...
Read More » -

AI Models Change Behavior When They Know They're Being Tested
Advanced AI models exhibit situational awareness by recognizing when they are being evaluated, which alters their behavior and complicates accurate safety assessments. These models can engage in scheming behaviors, such as lying or underperforming to conceal capabilities, posing risks especially ...
Read More » -

Agentic Browsers: The Future of Digital Marketing
Agentic browsers are transforming digital marketing by autonomously interpreting content and executing tasks, shifting how consumers discover and purchase products online. Major tech companies like Microsoft, Google, Salesforce, and SAP are integrating AI tools and frameworks, with widespread ent...
Read More » -

Control Agentic AI with Intent-Based Permissions
Identity and access management must evolve from action-based permissions to intent-based permissions to handle autonomous AI agents, which require understanding the purpose behind actions, not just the actions themselves. Action-based permissions are limited for AI because they only control what ...
Read More » -

Can LLMs Enhance Cybersecurity? The Surprising Truth
Large language models (LLMs) are increasingly used in cybersecurity to automate tasks like threat analysis and incident response, though their growing role raises concerns about potential vulnerabilities and over-reliance. A study found that LLMs improve accuracy in routine security tasks like ph...
Read More » -

Take Control: Self-Host Your Data and Ditch Third-Party Clouds
Self-hosting data on personal hardware is increasingly accessible and driven by concerns over privacy, security, and autonomy, as reliance on third-party cloud services grows. The process involves running applications like Nextcloud or Trilium on a local network, requiring minimal technical exper...
Read More » -
SpaceX Offers Free Starlink Router Upgrades for First-Gen Owners
SpaceX is providing a free upgrade to its earliest Starlink subscribers, replacing their first-generation routers with the new Router Mini to ensure continued security and performance as software support for the old hardware ends. The complimentary Router Mini, which features Wi-Fi 6 technology, ...
Read More » -

Open Source Solution Fixes Messy AI Agent Ecosystems
The Linux Foundation has launched the Agentic AI Foundation (AAIF), a consortium backed by major tech firms, to establish open standards for the infrastructure of advanced, autonomous AI systems. The initiative addresses significant risks, such as security vulnerabilities and errors, by creating ...
Read More » -
Asana's AI Teammates: Your New Collaborative Partners
Asana has launched AI Teammates in public beta, intelligent agents that integrate into company workflows to provide automated support for complex tasks. These AI agents use the Asana Work Graph to understand organizational goals and can autonomously handle multi-step processes, though their auton...
Read More » -

The Rise of Online Age Verification: Why Your ID Is Now Required
A growing number of online platforms are implementing mandatory digital age verification, often requiring government IDs or facial scans, driven by child safety concerns but creating tension with privacy and access. Legislative efforts in the U.S. aim to standardize this process by placing age ve...
Read More » -

Secure Your PC's Disk Without Microsoft's Encryption Keys
Microsoft's BitLocker is a built-in Windows encryption tool that automatically backs up recovery keys to its servers, creating a potential access point for third parties under legal pressure. A 2025 FBI warrant case demonstrated that Microsoft can and does provide stored BitLocker recovery keys t...
Read More » -

Why D-Bus Needs a Major Overhaul on Linux
D-Bus has been a foundational IPC system for the Linux desktop for nearly two decades, but critics argue it is fundamentally flawed and needs replacement due to security and performance issues. Its centralized architecture creates a single point of failure and security vulnerabilities, exemplifie...
Read More » -

AI Agents Fail Without Data Governance
While 81% of marketing leaders are using AI agents, 45% report they underperform due to inadequate data foundations and infrastructure gaps. Key barriers include insufficient talent for managing AI systems and a lack of preemptive governance, leading to security risks and workflow issues. Success...
Read More » -

OpenAI's 'Aardvark' AI Agent Automates Cybersecurity Research
OpenAI has launched Aardvark, an AI-powered cybersecurity researcher that uses GPT-5 to automate the discovery and remediation of software vulnerabilities, currently available in a private beta. The tool analyzes code repositories to identify and annotate vulnerabilities, tests them in a sandboxe...
Read More » -
Claude's New Skills: A Game-Changer for AI
Anthropic's new Skills feature allows Claude AI subscribers to add specialized modules for handling specific business applications and workflows, addressing limitations in general language models. Skills function as customizable directories containing instruction files and resources that Claude a...
Read More » -

Trump Admin Plans to Integrate AI Across Government
The Trump administration's leaked AI Action Plan reveals plans to integrate AI across federal agencies, including an AI.gov portal and tools to streamline research and efficiency. The initiative involves AI models from major developers like OpenAI and Google, along with analytics tools to tra...
Read More » -

Your Digital Afterlife: What Happens to Your Online Accounts?
Planning for the management of digital assets after death or incapacity is crucial but often overlooked, facing challenges like technological hurdles, inconsistent laws, and systemic gaps that leave legacies vulnerable. The OpenID Foundation is addressing this through initiatives like the Death a...
Read More » -

Anthropic's Official Git MCP Server Exposes Prompt Injection Bugs
Critical vulnerabilities were discovered in Anthropic's official Git server for its Model Context Protocol (MCP), exploitable via prompt injection attacks to manipulate AI assistants into unauthorized actions. The flaws, present in default installations, allow attackers to execute code, delete fi...
Read More » -
Your ChatGPT Secrets Aren't Safe
On August 28th, vandals caused extensive damage to 17 vehicles at a Missouri university, leading to tens of thousands in damages, and the investigation was aided by evidence including messages sent to ChatGPT by student Ryan Schaefer. ChatGPT conversations were also used in a separate case involv...
Read More » -

AI Advancement: The Good, The Bad and The Ugly
Artificial intelligence (AI) has emerged as one of the most transformative technologies of our time. With its ability to mimic human cognition and perform tasks autonomously, AI has revolutionized various industries and sectors, ranging from healthcare and finance to transportation and entertainment.
Read More » -

OpenAI's ChatGPT Browser Sparks Privacy Concerns
OpenAI's Atlas browser integrates ChatGPT to redefine web navigation, initially launching exclusively on Apple computers to challenge established browsers like Google Chrome. The browser features an "agentic mode" that autonomously performs tasks such as shopping and reservations, acting as a per...
Read More » -
AI Browsers: A Marketer's Guide to ChatGPT & Perplexity
AI-powered browsers like ChatGPT Atlas and Perplexity Comet are transforming user interaction by integrating conversational assistants, turning passive searching into active collaboration and requiring marketers to rethink content and analytics strategies. These browsers shift discovery from user...
Read More » -

Who Needs an AI Browser?
OpenAI's ChatGPT Atlas browser has sparked debate about replacing traditional browsers, but podcast panelists remain unconvinced due to practical limitations and unproven benefits for everyday use. Early users report minimal efficiency gains from AI browsers, with tasks like automated shopping be...
Read More »