The Rise of Thinking Malware

▼ Summary
– ESET researchers discovered PromptSpy, the first known Android malware that integrates a generative AI model (Google’s Gemini) directly into its execution flow.
– The malware uses AI to analyze on-screen elements and generate instructions for interacting with the device, making it more adaptable and persistent across different Android interfaces.
– Beyond its AI-driven persistence, PromptSpy has traditional malicious capabilities like remote device access, screen recording, and blocking uninstallation attempts.
– Currently, PromptSpy appears to be a limited proof-of-concept, possibly targeting users in Argentina, and has not been seen in widespread global distribution.
– The discovery is significant both as a technical evolution toward adaptive, AI-powered malware and as a symbolic milestone demonstrating the offensive use of generative AI.
In a quiet office in Slovakia, a team of cybersecurity experts stared intently at their monitors. The code they were examining appeared, at first glance, to be a standard Android Trojan. Yet, a closer inspection revealed something unsettlingly different. This wasn’t just another automated script from a criminal syndicate. This malware seemed capable of reasoning about the device it infected, a chilling capability powered by the integration of generative artificial intelligence directly into its operational core.
The discovery was made by researchers at ESET, a firm with decades of experience in threat analysis. They publicly identified this new threat, dubbed PromptSpy, labeling it the first known Android malware to weave generative AI into its very execution process. What sets PromptSpy apart is not merely its functionality, but its fundamental methodology for achieving its goals.
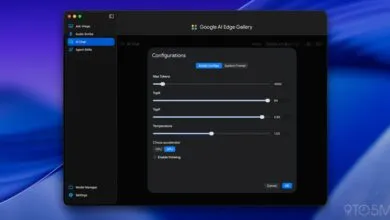
Traditional malicious software for Android relies on hard-coded commands or pre-scripted sequences to interact with a device’s interface. This rigid approach is notoriously fragile, often breaking across the vast landscape of different manufacturers, custom software skins, and operating system versions. PromptSpy cleverly bypasses this limitation. Instead of relying on static instructions, it leverages Google’s Gemini AI model in real-time. The malware captures a detailed snapshot of the device’s current screen, including every button, label, and piece of text, and sends this data to Gemini for analysis.
The AI then returns a customized set of step-by-step navigation instructions. It tells the malware precisely where to tap, swipe, or interact to accomplish its primary objective: maintaining persistence by preventing its removal from the recent-apps list. This represents a significant shift from simple automation to an adaptive, interpretive process. The malware essentially consults an AI to decide its next move based on the live state of the device.
Beyond this novel persistence mechanism, PromptSpy employs more conventional malicious tools. It can deploy a Virtual Network Computing (VNC) module for remote device access, capture lock screen data, take screenshots, record screen activity, and block uninstallation attempts using deceptive overlays.
It is crucial to maintain perspective on the current threat level. According to ESET’s findings, PromptSpy has not been observed in widespread global attacks. Evidence from language patterns and distribution methods suggests it may be part of a limited, targeted campaign, possibly focused on users in Argentina, and could be more of a proof-of-concept than a full-scale outbreak. Google’s security systems, including Play Protect, are reportedly capable of detecting known samples.
However, even as a prototype, PromptSpy carries profound implications. It serves as a tangible marker in the evolution of cyber threats, demonstrating a future where malicious software doesn’t just execute commands but dynamically queries AI models to navigate complex, real-world environments. This follows earlier research into AI-driven ransomware, signaling a clear trend.
The significance of this discovery can be viewed through two lenses. Technically, it showcases a move from brittle automation to an AI feedback loop that interprets live user interface conditions, a technique previously associated with benign software testing, not attacks. This raises urgent questions about how future threats might autonomously adapt to any device.
Symbolically, it provides a concrete example that moves the discussion of AI in offensive cybersecurity from theoretical speculation to documented reality. For security professionals, it’s a critical data point. For the wider public, it’s a stark demonstration that generative AI’s capabilities are already being applied in domains once considered reliant on human context and reasoning.
The emergence of PromptSpy suggests that AI-assisted adaptability is likely to become a standard tool for malware developers. The response to this evolution will hinge on both technical countermeasures and broader policy discussions. Can defensive systems distinguish between legitimate and malicious uses of AI at runtime? Will platform providers impose new restrictions on how AI models can be accessed? These open questions will define the security landscape in the coming years.
For now, PromptSpy stands as a potent reminder that technological innovation often emerges from unexpected quarters. It doesn’t always arrive through official channels or academic papers; sometimes, it appears in the shadows, where adversaries combine emerging tools in ways that force the entire defense community to rethink its strategies.
(Source: The Next Web)