Topic: Regulatory Compliance
-

Essential Compliance Features for Your Password Manager
Compromised passwords are a leading cause of security breaches, making a centralized enterprise password manager a strategic necessity for control and compliance with modern regulations. Regulations like GDPR, HIPAA, and industry frameworks like ISO 27001 mandate rigorous control over credential ...
Read More » -

Unlock Third-Party Assistants on iPhone With iOS 26.2
Apple will allow Japanese iPhone users to set third-party voice assistants like Gemini or Alexa as the default option for the Side Button, moving beyond Siri. This change is a direct response to Japan’s Mobile Software Competition Act, which mandates that platform holders must provide access to c...
Read More » -

2025: The Year Legal Battles Reshaped Gaming
The video game industry in 2025 is being reshaped by major legal and regulatory changes, particularly in mobile ecosystems where new rules are forcing open app stores and enabling alternative payment systems, leading to a fragmented global market. Monetization practices, especially in free-to-pla...
Read More » -

Top 10 Email Marketing Tools for Financial Services in 2025
Effective email marketing in financial services requires balancing personalized communication with strict regulatory compliance, using platforms that centralize client data and automate compliant follow-ups. Leading platforms like HubSpot, Salesforce, and Zoho cater to different segments, offerin...
Read More » -

Global Compliance Strategy: A Cross-Border Blueprint
Global compliance requires a forward-thinking strategy that integrates data protection with operational efficiency to avoid penalties and build trust. An ideal compliance platform must blend rigorous data protection with user-friendly design, ensuring scalability and adherence to international re...
Read More » -

Google Permits Prediction Market Ads With Strict Rules
Google will allow ads for regulated Prediction Markets in the U.S. starting January 21, but only federally authorized entities like CFTC-designated markets or NFA-registered brokerages are eligible. All advertisers must obtain specific certification from Google, ensuring ads and products comply w...
Read More » -

Apple Opens Brazil to Third-Party App Stores
Apple will allow third-party app stores and external payment systems on iPhones in Brazil starting next year, following a legal settlement with the country's antitrust authority. The company must implement these changes within 105 days or face significant fines, and any user warnings about third-...
Read More » -

Concentric AI Enhances Azure Security for Regulated Data
Concentric AI has expanded its Semantic Intelligence platform with a Private Scan Manager for Microsoft Azure, allowing sensitive data security operations to run entirely within a customer's private cloud infrastructure, following a similar offering for AWS. This solution is critical for highly r...
Read More » -

ImmuniWeb Boosts AI-Powered Security Testing & Compliance
ImmuniWeb's Q4 update focuses on identifying AI-specific vulnerabilities, including the OWASP Top 10 for LLMs, and expands capabilities for detecting exposed AI infrastructure and shadow IT assets. The platform enhances compliance testing for regulations like EU DORA, introduces new reporting fea...
Read More » -
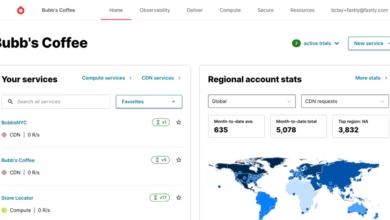
Fastly's New Dashboard Helps Businesses Make Climate-Smart Decisions
Fastly's sustainability dashboard provides businesses in Australia and New Zealand with detailed, actionable data on carbon emissions from using its edge computing services, helping them meet regulatory demands and optimize their environmental footprint. The tool offers comprehensive insights int...
Read More » -

Balancing AI Progress and Protection: A Strategic Roadmap
Australian businesses must balance rapid innovation with strong information governance to ensure data remains secure and compliant while pursuing growth. A strategic roadmap integrating information management into innovation processes is essential for maintaining compliance and enabling secure pr...
Read More » -

Mastering GenAI: Innovate Without the Risk
Global business leaders are embracing generative AI for its transformative potential and significant returns, with 78% of organizations using AI and achieving an average return of $3.70 per dollar invested. Despite the benefits, there is growing apprehension about AI-driven risks, including data ...
Read More » -

Tame Unstructured Data with Policy-Driven Management
Unstructured data, which constitutes most digital information, is difficult to manage due to its volume, spread across systems, and complex formats, hindering business value extraction. Organizations must shift from manual, reactive data management to a proactive, policy-based model, using automa...
Read More » -

Rulebase: The AI Coworker for Fintech, Backed by Y Combinator
Rulebase is a fintech startup focusing on back-office automation, using AI to streamline compliance, dispute resolution, and quality assurance in financial institutions. Founded by Gideon Ebose and Chidi Williams, the company secured $2.1 million in pre-seed funding and has achieved significant c...
Read More » -

50 Companies' Biggest Cloud Identity Security Mistakes
Businesses face significant cloud identity security risks, with an average of 40 high-risk control failures per organization, exposing them to breaches and compliance failures. Common vulnerabilities include missing multi-factor authentication, excessive permissions, outdated credentials, and poo...
Read More » -
From Traditional to AI: The Evolution of Credit Risk Analysis
Credit risk analysis has evolved from manual methods to AI-driven systems using real-time data to address global debt, regulations, and data growth. The shift includes digitization, alternative data sources, and machine learning for faster, more accurate, and inclusive risk assessments. Challenge...
Read More » -
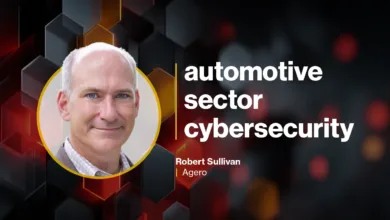
Go Beyond Checklists: Build a Mature Automotive Cybersecurity Program
A mature automotive cybersecurity program requires a foundation in established frameworks like ISO, but must go beyond compliance by developing a tailored risk management strategy that addresses unique threats and deploys proactive controls across the enterprise. Comprehensive threat visibility, ...
Read More » -

Ro's CISO: Securing Telehealth Data Flows
The rapid growth of telehealth creates a complex data flow across cloud and third-party platforms, demanding a dynamic, continuous security strategy that goes beyond static compliance to protect patient privacy. A core vulnerability is the frequent lack of universal data classification, making it...
Read More » -

Who Else Has Access to Your Wearable's Heartbeat Data?
The proliferation of smartwatches and connected medical devices enables remote health monitoring and personalized care, but it also introduces significant security vulnerabilities due to the constant flow of sensitive data. Ambiguity in health data ownership and sharing practices raises privacy c...
Read More » -

Nutanix Cloud Clusters Now Available on OVHcloud
Nutanix Cloud Clusters (NC2) on OVHcloud offers businesses in Europe and the Middle East a hybrid multicloud platform that emphasizes European data sovereignty, regulatory compliance, and sustainable infrastructure. The partnership provides a flexible and trustworthy alternative for workload migr...
Read More » -

Mastering GenAI: Innovate Boldly, Manage Risk Wisely
Generative AI is widely adopted by businesses for innovation and efficiency, but its rapid integration introduces significant security risks like data leaks and a lack of specific protocols. High-profile incidents, such as breaches at JedAI and Samsung, demonstrate vulnerabilities including shado...
Read More » -

Unlock Sovereign AI with Cloudian's NVIDIA-Powered Platform
Organizations can deploy sovereign AI infrastructure within national borders using Cloudian's integrated platforms, combining S3-compatible storage with NVIDIA's technology to maintain data control and comply with regulations. Cloudian offers two key platforms: HyperStore for on-premises AI data ...
Read More » -

Healthcare's Silent Cybersecurity Crisis
Healthcare organizations significantly underestimate their cybersecurity vulnerabilities despite facing increasingly sophisticated digital threats, creating a dangerous gap between perceived and actual security readiness. The reliance on technology for clinical outcomes means cybersecurity breach...
Read More » -

Europe's Battery Startups: How to Compete with Asian Giants
The global battery market is projected to reach $400 billion by 2030, with European startups advised to leverage unique strengths like proximity to customers, regulatory expertise, and agility rather than competing on price. European firms should target specialized niches such as aerospace, medic...
Read More » -

Supply Chain Shifts Challenge CPS Security Strategies
Cyber-physical systems face heightened risks due to supply chain instability and regulatory changes, with 46% of organizations experiencing third-party breaches in the past year. External regulations, rather than internal assessments, are driving security strategies, and 76% of organizations expe...
Read More » -

The Hidden Cost of a Security Breach
Companies are shifting security budgets reactively after breaches, but this emergency spending is far more costly than proactive investment, often exceeding it by a factor of nine. The rise of new attack vectors, especially targeting SaaS data, increases breach likelihood and financial damage, ye...
Read More » -

Secure Your Data Offline with Acronis Cyber Protect Local
Acronis Cyber Protect Local is an all-in-one on-premises platform that integrates data backup, cybersecurity, and endpoint management for IT and OT environments, ensuring data sovereignty and reducing complexity. It supports legacy systems and modern hypervisors, offering broad compatibility, AI-...
Read More » -

Microsoft 365 Copilot to Process UAE Data Locally
Microsoft will launch local data processing for Microsoft 365 Copilot in the UAE by early 2026, hosted in Dubai and Abu Dhabi data centers to enhance security and performance for organizations. This initiative supports the UAE's National AI Strategy and digital sovereignty by ensuring data remain...
Read More » -

Judge Rules Tesla Misled Buyers on Self-Driving Tech
A California judge ruled Tesla's marketing of its Autopilot and Full Self-Driving systems is misleading, and the state's DMV has adopted this ruling, threatening a 30-day sales license suspension if advertising is not corrected. The DMV found Tesla's product names violate state law by implying a ...
Read More » -

MCP Security Blind Spots: The API Risk
The Model Context Protocol (MCP) introduces unique security risks because it injects executable text directly into AI models, unlike standard APIs, and lacks built-in trust or version control, making conventional security frameworks inadequate. Organizations face significant governance blind spot...
Read More » -

ID-Pal's ID-Detect Now Fights Deepfakes and Synthetic IDs
ID-Pal has upgraded its ID-Detect system to include advanced protection against AI-generated deepfakes and synthetic identity documents, addressing escalating fraud risks faced by financial institutions. The enhanced system defends against four types of presentation attacks, such as screen replay...
Read More » -

Exposure Management: The New Boardroom Test
Cybersecurity is now a critical board-level concern due to regulatory, investor, and reputational pressures, with exposure management providing a framework to address the gap between investment and escalating breaches. Exposure management shifts focus from counting resolved alerts to continuously...
Read More » -

Sarmad Launches Thamar to Simplify Saudi Investor Services
Sarmad has launched thamar, a digital platform designed to modernize investor services for asset management firms in Saudi Arabia, aligning with Vision 2030 to enhance financial digitization. The platform streamlines operations by connecting asset managers with distributors, digitizing workflows,...
Read More » -

DataLocker Enhances Security with DL GO & MySafeConsole
DataLocker has launched the DL GO encrypted USB drive and MySafeConsole cloud platform, offering enterprise-level security features at an accessible price for individuals and small businesses. The DL GO drive uses AES-256 XTS hardware encryption, supports biometric authentication, and has a rugge...
Read More » -

Arcee Launches Custom AI Model AFM-4.5B for Enterprises
Arcee.ai launched AFM-4.5B, a 4.5-billion-parameter AI model for enterprises, offering free limited access for smaller businesses under a custom licensing agreement. The model is compact, instruction-tuned for tasks like chat and creative writing, and supports diverse deployment environments, wit...
Read More » -

API Security: Why CISOs Must Act Now Before Regulations Hit
Businesses face increasing risks from unprotected APIs, exposing sensitive data and corporate assets due to widespread security gaps in API management. Many organizations unknowingly leak private data through poorly secured APIs, making them easy targets for cybercriminals, as seen in real-world ...
Read More » -

Meta to Automate Product Risk Evaluations for Efficiency
Meta is developing an AI system to automate up to 90% of product risk assessments for platforms like Instagram and WhatsApp, aiming to speed up updates while ensuring compliance. The AI will analyze questionnaires from product teams to flag potential risks, though critics warn reduced human overs...
Read More » -

ID Verification Laws Are Creating New Security Breaches
New ID verification laws are forcing businesses to collect sensitive personal data like government IDs, often without adequate security infrastructure, conflicting with the cybersecurity principle of minimal data collection. A Discord data breach exposed government ID images collected for age ver...
Read More » -

RecordPoint Names Brett Hooker as Inaugural Chief Operating Officer
RecordPoint has appointed Brett Hooker as its first Chief Operating Officer to support global expansion and operational scaling amid rising demand for data governance solutions. Hooker brings extensive experience from TechnologyOne and will oversee end-to-end operations, enhancing systems and ali...
Read More » -
Unlock Customer Sentiment & Risk Hidden in Your CRM Emails
Generative AI transforms inbound CRM email analysis by uncovering customer sentiment and risks, shifting focus from traditional outbound metrics to understanding actual communication content and emotional tone. Natural language processing reveals nuanced customer emotions, pain points, and buying...
Read More » -

Excite and Nuix Land $1.35M Contract Deal
Excite Technology Services has secured a $1.35 million, 12-month contract to provide Nuix software solutions to an Australian Regulator through its subsidiary CBIT. The agreement involves delivering the Nuix Neo Discover platform to support the Regulator's discovery, workflow automation, and fore...
Read More » -

Spoor's Bird Monitoring AI Software Takes Flight
Spoor's AI-powered software uses cameras to detect and identify birds with 96% accuracy, helping industries like wind farms minimize avian collisions through operational adjustments. The technology addresses a regulatory gap by replacing outdated manual monitoring, and its applications are expand...
Read More » -

13 Must-Check Google Ads Settings for International PPC Success
Successfully launching Google Ads in a new country requires a fundamental strategic shift, moving beyond simple translation to meticulously align account settings like location targeting, currency, and ad scheduling with local market realities. Critical technical adjustments include setting preci...
Read More » -

AI-Powered Blackdot Videris Automates OSINT & Risk Detection
Blackdot Solutions has launched Videris Automate, an AI-powered platform that automates investigations and screening to help companies identify threats, uncover hidden relationships, and make faster decisions. The platform accelerates workflows by automating manual tasks, enabling efficient analy...
Read More » -

F5 Acquires CalypsoAI to Secure Generative AI Systems
F5 is acquiring CalypsoAI for $180 million to enhance its security offerings with specialized capabilities for protecting generative AI systems against emerging threats. The acquisition aims to integrate CalypsoAI's technology into F5's platform, providing real-time threat defense, data security,...
Read More » -

13 Must-Check Google Ads Settings for International PPC Success
Expanding Google Ads internationally requires meticulous account configuration, including precise location targeting to focus on users physically present in the target market, to avoid inefficient spending and ensure sustainable growth. Key technical adjustments are essential, such as aligning ad...
Read More » -

AI Is Making Banking More Personal
AI is transforming banking by enabling highly personalized customer service through data analysis, moving beyond basic digital access to anticipate needs and build loyalty. Successful AI deployment requires balancing innovation with responsibility, respecting brand heritage and consumer privacy w...
Read More » -

Secure Energy Operations: Password & Continuity Management
Energy infrastructure faces a unique cybersecurity challenge: it must enforce strong authentication to prevent catastrophic physical disruptions, while ensuring 24/7 operational continuity where strict policies can be dangerous. The sector is under increasing threat from sophisticated attacks, an...
Read More » -

Waymo robotaxi investigated for driving around school bus
The NHTSA is investigating a Waymo autonomous vehicle for allegedly failing to stop for a school bus with activated red lights in Atlanta, raising concerns about its compliance with traffic safety laws. Waymo attributed the incident to a sensor failure that missed the bus's signals and has since ...
Read More » -
The 'Papers, Please' Internet Is Here
Global mandatory online age verification is rapidly expanding from initial UK proposals to worldwide legislation, with the EU, Australia, and the U.S. Supreme Court enabling such requirements. Implementation reveals significant challenges including security vulnerabilities, loopholes, VPN usage, ...
Read More »