Urgent: Patch Windows SMB Flaw Being Actively Exploited

▼ Summary
– CVE-2025-33073 is a Windows SMB Client vulnerability that Microsoft patched in June 2025 and is now being actively exploited by attackers.
– The vulnerability allows for privilege escalation, enabling attackers to gain SYSTEM privileges on vulnerable Windows systems through a malicious SMB script.
– CISA has added this flaw to its Known Exploited Vulnerabilities catalog and requires US federal agencies to remediate it by November 10, 2025.
– Researchers note that the flaw bypasses NTLM reflection mitigations and functions as an authenticated remote command execution vulnerability, not just a privilege escalation.
– CISA also mandated mitigation for other vulnerabilities, including an Apple flaw, an Oracle E-Business Suite SSRF issue, and two Kentico Xperience authentication bypasses.
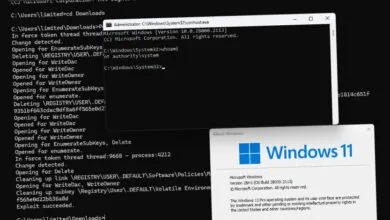
A critical security flaw within the Windows SMB Client, identified as CVE-2025-33073, is now under active exploitation by malicious actors. This vulnerability, for which Microsoft released a patch in June 2025, has been officially confirmed by the Cybersecurity and Infrastructure Security Agency (CISA). The agency has placed the flaw on its Known Exploited Vulnerabilities catalog, signaling that attacks are occurring in the wild based on reliable evidence.
The nature of CVE-2025-33073 involves privilege escalation, giving attackers the ability to obtain SYSTEM-level privileges on affected Windows or Windows Server installations. Microsoft explains that exploitation requires an attacker to run a maliciously designed script. This script forces the targeted computer to initiate an SMB connection back to the attacker’s server and authenticate. Once this connection is established, the malicious server can compromise the communication protocol. Alternatively, an attacker might trick a user into manually executing the harmful script.
When Microsoft first issued the fix, they noted the vulnerability had been publicly disclosed but was not known to be actively exploited at that time. The following day, the company credited its discovery to a team of security researchers from various organizations, including CrowdStrike, Synacktiv, GuidePoint Security, BNP Paribas, SySS GmbH, RedTeam Pentesting GmbH, and Google Project Zero.
Several of these researchers have since shared technical insights into the vulnerability. For instance, experts from Synacktiv pointed out that it bypasses NTLM reflection mitigations and permits an authenticated remote attacker to run arbitrary commands with SYSTEM privileges on any machine where SMB signing is not enforced. They also emphasized that although Microsoft classifies CVE-2025-33073 as a privilege escalation issue, it effectively functions as an authenticated remote command execution vulnerability. Proof-of-concept exploit code has been made available by other researchers, increasing the risk of widespread attacks.
In line with standard procedure, CISA has not disclosed specifics about the ongoing attacks but has instructed all US Federal Civilian Executive Branch agencies to apply the necessary patches by November 10, 2025. Alongside this directive, agencies must also address several other security vulnerabilities within the same timeframe.
These include an older vulnerability impacting Apple’s iOS and macOS (CVE-2022-48503), a recently patched Server-Side Request Forgery (SSRF) flaw in Oracle E-Business Suite (CVE-2025-61884) that may have been used by the Cl0p ransomware group, and two authentication bypass issues (CVE-2025-2746, CVE-2025-2747) found in Kentico Xperience Staging Sync Server, which were uncovered and disclosed by researchers at watchTowr.
Staying informed about emerging threats is essential for maintaining cybersecurity. Subscribing to breaking news alerts ensures you receive immediate updates on significant breaches, newly discovered vulnerabilities, and other critical security developments.
(Source: HelpNet Security)