New Linux Exploit Grants Hackers Root Access to Millions of Computers
▼ Summary
– The critical Linux vulnerability CVE-2026-31431 (CopyFail) allows unprivileged users to gain root access, with exploit code publicly released on Wednesday after a five-week private disclosure to the Linux kernel security team.
– The exploit works reliably across multiple Linux distributions, including Ubuntu 22.04, Amazon Linux 2023, SUSE 15.6, and Debian 12, using a single Python script with no modification needed.
– CopyFail poses severe risks in shared infrastructure, such as breaking out of Kubernetes containers, compromising multi-tenant systems, and abusing CI/CD workflows.
– The vulnerability originates from a logic flaw in the kernel’s crypto API, where the authencesn AEAD template fails to copy data, writing 4 bytes past the destination buffer without restoring them.
– Security experts describe CopyFail as the worst make-me-root Linux kernel vulnerability in recent times, comparable to Dirty Pipe (2022) and Dirty Cow (2016), both of which were actively exploited.
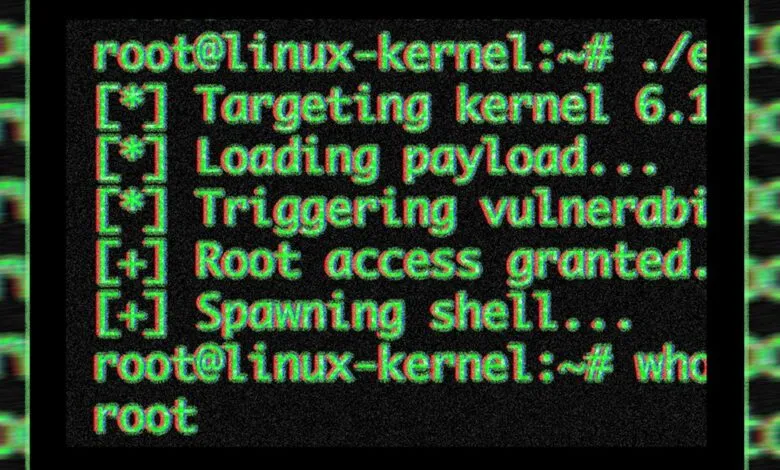
Publicly available exploit code for a critical, largely unpatched Linux vulnerability is now in the wild, enabling attackers to gain root access across virtually all Linux distributions. The development has sparked urgent warnings as security teams race to prevent devastating breaches inside data centers and on personal devices alike.
Researchers from security firm Theori published the exploit code and vulnerability details on Wednesday evening, five weeks after privately reporting the flaw to the Linux kernel security team. While the kernel team addressed the issue in versions 7.0, 6.19.12, 6.18.12, 6.12.85, 6.6.137, 6.1.170, 5.15.204, and 5.10.254, most Linux distributions had not integrated those patches by the time the exploit went public.
A Single Script to Hack Them All
The flaw, tracked as CVE-2026-31431 and named CopyFail, is a local privilege escalation vulnerability. This class of bug lets unprivileged users elevate their access to administrator-level control. What makes CopyFail especially dangerous is that the exploit code released Wednesday works across all vulnerable distributions with zero modification. An attacker can use it to compromise multi-tenant systems, escape containers built on Kubernetes or similar frameworks, and inject malicious pull requests that push the exploit through CI/CD pipelines.
“‘Local privilege escalation’ sounds dry, so let me unpack it,” wrote researcher Jorijn Schrijvershof on Thursday. “It means: An attacker who already has some way to run code on the machine, even as the most boring unprivileged user, can promote themselves to root. From there they can read every file, install backdoors, watch every process, and pivot to other systems.”
Schrijvershof noted that the same Python script released by Theori works reliably on Ubuntu 22.04, Amazon Linux 2023, SUSE 15.6, and Debian 12. He continued: “Why does that matter on shared infrastructure? Because ‘local’ covers a lot of ground in 2026: every container on a shared Kubernetes node, every tenant on a shared hosting box, every CI/CD job that runs untrusted pull-request code, every WSL2 instance on a Windows laptop, every containerised AI agent given shell access. They all share one Linux kernel with their neighbors. A kernel LPE collapses that boundary.”
The realistic threat chain is straightforward. An attacker exploits a known WordPress plugin vulnerability to gain shell access as www-data. They then run the CopyFail proof-of-concept code. Within seconds, they become root on the host. Every other tenant becomes immediately reachable. As Schrijvershof explained, “The vulnerability does not get the attacker onto the box; it changes what happens in the next ten seconds after they land there.”
The Root Cause: A Logic Flaw
CopyFail originates from a “straight-line” logic flaw in the kernel’s crypto API. Many exploits rely on race conditions or memory corruption flaws, which often fail to succeed consistently across different kernel versions or distributions, and sometimes even on the same machine. Because CopyFail exploits a pure logic flaw, “reliability isn’t probabilistic, and the same script works across distributions,” wrote researchers from Bugcrowd. “No race window, no kernel offset.”
The vulnerability earns its name because the authencesn AEAD template process, used for IPsec extended sequence numbers, fails to copy data when it should. Instead, it “uses the caller’s destination buffer as a scratch pad, scribbles 4 bytes past the legitimate output region, and never restores them,” Theori explained. “The ‘copy’ of the AAD ESN bytes ‘fails’ to stay inside the destination buffer.”
The Worst Linux Vulnerability in Years
Security experts have described CopyFail as one of the most severe “make-me-root” vulnerabilities in the Linux kernel in recent memory. The last comparable threats were Dirty Pipe in 2022 and Dirty Cow in 2016, both of which were actively exploited in the wild. Given the ease of exploitation and the broad attack surface, defenders are now in a race to patch systems before attackers can leverage CopyFail for widespread compromise.
(Source: Wired)




