Topic: system integrity
-

Microsoft Boosts Windows Security with App Transparency
Microsoft is introducing two key security features: **User Transparency and Consent** for explicit user permission prompts and logging, and **Windows Baseline Security Mode** to restrict execution to trusted, signed applications by default. These updates are part of Microsoft's broader **Secure F...
Read More » -

Rethinking Cybersecurity from the Silicon Up
Traditional reactive cybersecurity, focused on software patches and detection, is insufficient against modern threats that target deeper hardware and firmware layers. A Hardware Root of Trust (HRoT) embedded in silicon provides a proactive, tamper-resistant foundation by actively validating hardw...
Read More » -
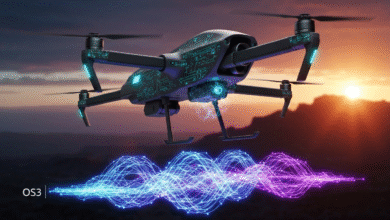
Mobilicom Launches Secure AI Drone Autonomy System
Mobilicom has launched the Secured Autonomy Compute PRO-AT, a secure AI drone autonomy system that integrates its OS3 cybersecurity software with Aitech's rugged NVIDIA-based AI supercomputers to support larger drones like those in U.S. DoD Groups 2 and 3. The system combines high-performance AI ...
Read More » -

Panama Economy Ministry Confirms INC Ransomware Attack
The Ministry of Economy and Finance in Panama experienced a cybersecurity incident on a single workstation, but core systems and operations remain unaffected. The INC Ransom group has claimed responsibility, alleging they stole over 1.5 terabytes of sensitive data including financial records and ...
Read More » -

Portugal Exempts Security Researchers From Cybercrime Law
Portugal has enacted a new law creating a legal safe harbor for good-faith security researchers, protecting them from prosecution for activities aimed at uncovering and responsibly disclosing software vulnerabilities. To qualify, researchers must follow strict rules: they cannot seek extra econom...
Read More »