All Related Articles for: Find Security Flaws in Python Code with Bandit
Found 353 articles related to this post based on shared entities and topics.
-
 December 3, 2025
December 3, 2025AI Supply Chains at Risk from Critical PickleScan Flaws
Researchers discovered three critical zero-day vulnerabilities (CVSS 9.3) in…
Read More » -
 December 3, 2025
December 3, 2025Nvidia Unveils Open AI Models for Autonomous Driving Research
Nvidia has launched the open-source Alpamayo-R1 model, a vision…
Read More » -
 December 2, 2025
December 2, 2025MCP Security Blind Spots: The API Risk
The Model Context Protocol (MCP) introduces unique security risks…
Read More » -
 December 2, 2025
December 2, 2025A Step-by-Step Guide to Implementing Zero Trust
Zero trust security shifts from assuming internal network trust…
Read More » -
 December 2, 2025
December 2, 2025MKBHD Discontinues His Wallpaper App
Tech reviewer MKBHD is shutting down his premium wallpaper…
Read More » -
 November 28, 2025
November 28, 2025Top Cybersecurity Open-Source Tools: November 2025
Open-source cybersecurity tools are increasingly popular for providing robust,…
Read More » -
 November 28, 2025
November 28, 2025What CISOs Must Tell the Board About Cyber Risk
CISOs must communicate cybersecurity risks in business terms, focusing…
Read More » -
 November 28, 2025
November 28, 2025Heineken CISO: How a Risk-First Mindset Drives Innovation
CISOs must shift from technical oversight to strategic partnership…
Read More » -
 November 28, 2025
November 28, 2025Unleash DeepTeam: Open-Source LLM Red Teaming
DeepTeam is an open-source framework that rigorously tests large…
Read More » -
 November 27, 2025
November 27, 2025Code Formatting Sites Leak User Secrets and Credentials
Popular online code formatting platforms like JSONFormatter and CodeBeautify…
Read More » -
 November 27, 2025
November 27, 2025New npm Worm Threatens Software Supply Chain
A sophisticated worm called Shai-Hulud is actively stealing developer…
Read More » -
 November 26, 2025
November 26, 2025AI Meltdown: Reshaping Enterprise Expectations
The enterprise AI industry lacks a major failure to…
Read More » -
 November 26, 2025
November 26, 2025Beware: Malicious Blender Files Spreading StealC Malware
A Russian-linked cyberattack is distributing the StealC V2 malware…
Read More » -
 November 26, 2025
November 26, 2025500 npm Packages Infected by Shai-Hulud Malware Leaking Secrets
Over 500 npm packages, including popular tools like Zapier…
Read More » -
 November 25, 2025
November 25, 2025Secure Your Cloud with cnspec: Open-Source Policy & Security
cnspec is an open-source tool that provides unified security…
Read More » -
 November 25, 2025
November 25, 2025Quantum Encryption Strains Satellite Tech to the Brink
Quantum computing threatens global satellite network security, requiring an…
Read More » -
 November 23, 2025
November 23, 2025Microsoft Open Sources Classic Zork Games I, II & III
Microsoft has open-sourced the classic Zork trilogy under the…
Read More » -
 November 22, 2025
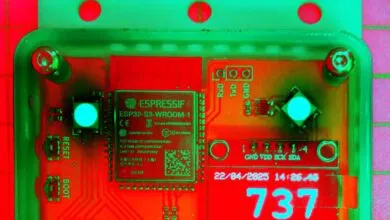
November 22, 2025Hackers Build a Literal Anti-Virus at Security Conference
Elevated carbon dioxide levels impair cognitive function and prolong…
Read More » -
 November 21, 2025
November 21, 2025IBM Engineer Takes Quantum Computing From Lab to Reality
Quantum computing is advancing from theory to practical use,…
Read More » -
 November 21, 2025
November 21, 2025Uncover Hidden DevOps Data Risks and How to Fix Them
DevOps practices accelerate innovation but introduce significant data vulnerabilities,…
Read More »