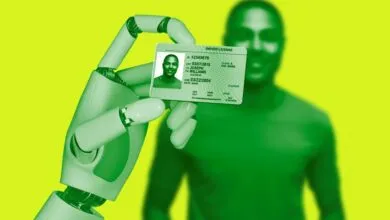
ID Verification Laws Are Creating New Security Breaches

▼ Summary
– ID laws now force organizations to store sensitive data they may not want but must protect, conflicting with the traditional cybersecurity principle of minimal data collection.
– A Discord data breach exposed government ID images collected for age verification, highlighting the security risks of mandated data storage.
– Organizations face severe consequences from breaches, including regulatory fines, lawsuits, and reputational damage, which can be devastating for small businesses.
– Managed service providers (MSPs) are particularly vulnerable due to handling data for multiple clients with complex, multi-tool systems that create security gaps.
– Integrating cybersecurity, data protection, and endpoint management into a single platform reduces attack surfaces and simplifies security for MSPs.
For businesses navigating today’s complex digital environment, the proliferation of ID verification laws presents a significant security challenge. Cybersecurity experts have traditionally advised collecting only essential data to minimize risk. However, new legal requirements are compelling organizations to amass vast quantities of highly sensitive information, including government-issued identification documents, often without the robust infrastructure needed to protect it adequately.
A recent incident involving the popular platform Discord highlights this growing problem. In late 2025, the company reported that a cyberattack had targeted one of its third-party customer support vendors. The breach exposed standard support data like email addresses and user messages. More alarmingly, it also compromised a trove of government ID images. These documents were collected from users who had submitted them to appeal account suspensions related to being underage, a direct result of compliance with age verification legislation.
This scenario underscores a difficult predicament for companies. The intention behind these laws, to shield minors from harmful online content, is undoubtedly sound. Yet the practical outcome forces businesses into a precarious position. They are now legally obligated to gather and store the most sensitive forms of personally identifiable information (PII), regardless of their desire or capacity to secure it effectively. The foundational security principle of minimal data collection is rendered obsolete when regulations demand the opposite.
The repercussions of this shift are widespread. Virtually any organization serving the public, from healthcare providers and financial institutions to e-commerce sites and schools, could fall under mandates requiring the collection of sensitive documents. Every new database of driver’s licenses or passports becomes a tempting target for cybercriminals. When a breach inevitably occurs, the fallout is severe, encompassing regulatory fines, costly lawsuits, reputational harm, and a critical erosion of customer trust. For small and medium-sized businesses, a single significant data leak involving PII can be catastrophic.
Managed Service Providers (MSPs) are particularly affected by this trend. By their nature, MSPs handle sensitive data for a diverse range of clients, each with unique compliance needs. A security incident at an MSP doesn’t just impact one company; it can simultaneously jeopardize the data of dozens or even hundreds of client organizations. The conventional MSP technology setup, which often involves a patchwork of disconnected security tools, only intensifies this vulnerability. Using separate systems for backup, endpoint protection, and vulnerability management creates multiple potential entry points for attackers and leads to dangerous security gaps where data may be unprotected.
The most effective strategy for mitigating these risks is not to add more point solutions but to consolidate them. MSPs can dramatically enhance their security posture by adopting a natively integrated platform that combines cybersecurity, data protection, and endpoint management into a single, unified solution. This approach eliminates the vulnerabilities inherent in managing multiple vendors and tools. With all functions operating through a single agent and management console, there are no weak handoff points where data can be exposed. This consolidation also reduces administrative overhead, provides comprehensive visibility from a single interface, and minimizes the attack surface by reducing the number of potential entry points.
In an era where data collection is often legally mandated, the old rules of cybersecurity are being rewritten. The breach involving Discord’s partner is a stark reminder of the new threats created by ID laws. For MSPs tasked with safeguarding this ever-growing pool of sensitive client information, leveraging every available advantage is crucial. Adopting a streamlined, integrated security platform is no longer a mere option but a fundamental requirement for survival and resilience.
(Source: Bleeping Computer)