Traditional security tools are inadequate for detecting risks like prompt injection, data leakage, and model manipulation when enterprises deploy generative…
Read More »Cybersecurity
Keep up with cybersecurity threats, data privacy, hacking incidents, and digital protection strategies. Learn about security tools, expert insights, and best practices to safeguard your online presence.
Researchers have developed a new surveillance technique called FROST that uses timing measurements of SSD interactions to monitor which websites…
Read More »Certain Motorola smartphones have been found secretly injecting affiliate referral codes into Amazon app links without user knowledge or consent.…
Read More »The ShinyHunters extortion group breached 7-Eleven's internal systems in April 2026, stealing personal data of over 185,000 individuals, including names,…
Read More »F-Secure Internet Security provides cross-platform protection against viruses, ransomware, spyware, and scams, with features including device scanning, scam and browsing…
Read More »The article lists 10 diverse cybersecurity job openings worldwide, including roles like Application Security Engineer, CISO, Red Team Operator, and…
Read More »The FBI made early arrests under the Take It Down Act by simply browsing porn sites and searching hashtags like…
Read More »The original 2011 Secure Boot certificates will expire by June 2026, and Microsoft is transitioning to new 2023 certificates via…
Read More »NetEase permanently banned hundreds of players caught using or distributing cheats in "Marvel Rivals", publicly naming them (with censored usernames)…
Read More »Cisco warns that AI will accelerate vulnerability discovery, worsening the already overwhelming volume of findings that security teams must triage…
Read More »The FBI warns about Kali365, a phishing-as-a-service platform that targets Microsoft 365 accounts by abusing OAuth device code authentication to…
Read More »PeerSpot has ranked Safeguard by One Identity as the top solution for non-human identity (NHI) management, highlighting the urgent need…
Read More »State governments are launching initiatives like cybersecurity clinics, regional security operations centers (RSOCs), and state cyber corps to protect local…
Read More »The Dutch government blocked Kyndryl's €100 million acquisition of Solvinity, citing national security and digital sovereignty concerns over foreign control…
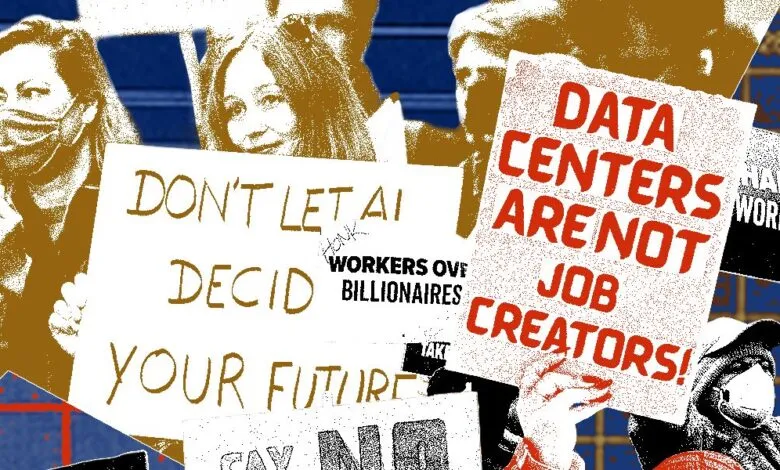
Read More »Federal intelligence agencies and U.S. law enforcement have identified "anti-technology extremists" as a new domestic threat, with surveillance priorities shifting…
Read More »A critical vulnerability (CVE-2026-48710, "BadHost") in the Starlette framework, which receives 325 million weekly downloads, allows hackers to easily infiltrate…
Read More »After over 2,000 hours of government-enforced blackouts in 2026, Iran’s internet is slowly returning at minimal levels, triggered by attacks…
Read More »The Dutch government blocked Kyndryl's acquisition of cloud provider Solvinity over national security concerns, as Solvinity hosts DigiD, the Netherlands'…
Read More »The 2026 Verizon DBIR reports that vulnerability exploitation has overtaken stolen credentials as the primary breach vector (31% of breaches),…
Read More »The US and Israel’s attacks on Iran three months ago have triggered an open-ended regional conflict with severe economic and…
Read More »