Microsoft Sentinel’s AI Cybersecurity Strategy
▼ Summary
– AI is reshaping cybersecurity by creating both new threats and new tools for mitigation.
– Microsoft has upgraded its Sentinel platform to operate more autonomously using graph-based context for threat response.
– Security Copilot agents now leverage graph-based reasoning to correlate alerts, enrich context, and automate routine tasks.
– Microsoft introduced the Sentinel Model Context Protocol server and made the Sentinel data lake generally available for integration and data storage.
– Microsoft positions these upgrades as part of a broader paradigm shift toward human-AI collaboration in cybersecurity defense.
The rapid evolution of artificial intelligence is fundamentally reshaping the cybersecurity domain, simultaneously introducing sophisticated new threats while also powering advanced defense mechanisms. Microsoft is strategically positioning itself at the forefront of this shift, aiming to become the indispensable partner for security professionals navigating this new reality. The company’s latest move involves a significant upgrade to its Sentinel platform, a Security Information and Event Management (SIEM) system designed for threat monitoring and response.
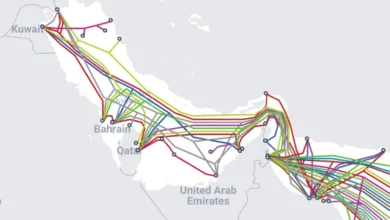
A core enhancement announced for Sentinel is its adoption of a “graph-based” operational context. This methodology treats a computer network as a unified web of interconnected digital pathways, much like points on a coordinate grid. When a security threat emerges at any node within this system, it can be instantly evaluated based on its relationships and potential impact across the entire network. This allows the platform to map the trajectory of a threat, tracing its origins and predicting its potential future movements.
These graph-based capabilities are engineered to empower Microsoft’s Security Copilot agents. Building on Sentinel’s graph-based context, Security Copilot agents can now reason more effectively across your environment — correlating alerts, enriching context with relationships, prioritizing by impact, and automating common actions, explained Vasu Jakkal, Corporate Vice President of Microsoft Security. The overarching goal is to transition security workflows from manual processes to agent-led automation. This shift enables agents to handle routine tasks, allowing human analysts to dedicate their expertise to strategic decision-making and proactive threat hunting.
Further expanding its ecosystem, Microsoft also introduced the Sentinel Model Context Protocol (MCP) server. This tool allows for the integration of custom agents developed on platforms like Visual Studio Code directly into the Sentinel environment. Additionally, the company confirmed that its Sentinel data lake, a centralized repository for storing vast amounts of structured and unstructured data, has moved from its preview phase to general availability.
Microsoft is promoting these upgrades as more than just incremental product improvements; they are presented as foundational components for a new era of cybersecurity defense. This new paradigm is characterized by a collaborative partnership between human intelligence and artificial intelligence, working in tandem to counter increasingly complex threats. As other technology firms also respond to the novel security challenges posed by AI agents, initiatives like the collaboration between Meta and CrowdStrike to establish performance benchmarks for AI security tools highlight the industry-wide effort to navigate this transformative period.
(Source: ZDNET)