Major MediaTek Flaw Impacted More Android Phones Than Thought
▼ Summary
– A security vulnerability allowed sensitive data like PINs and crypto wallet seeds to be extracted from a Nothing phone using a MediaTek chip.
– The security firm Trustonic disputes claims that its software was the source of the vulnerability on MediaTek processors.
– Trustonic states the issue is specific to MediaTek’s platform, as its software operates securely on other chipset vendors.
– MediaTek issued a fix for the vulnerability in January 2026, but the full scope of affected devices remains unclear.
– The vulnerability’s impact may be broader than initially thought, potentially affecting various Android devices and security systems.
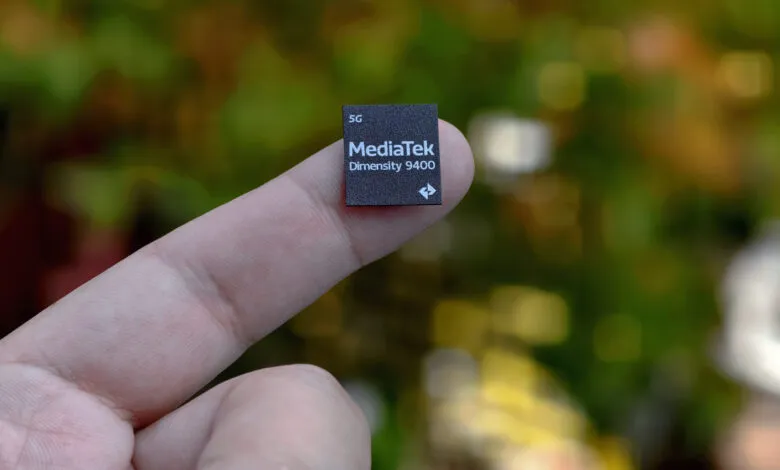
A recently identified security flaw in MediaTek processors may have impacted a far greater number of Android smartphones than first reported. This vulnerability, which allowed for the extraction of sensitive data like PINs and cryptographic keys in under a minute, was initially linked to a specific security component. However, new statements suggest the problem’s roots and reach are broader, raising concerns for device manufacturers and users alike.
The weakness was first uncovered by security researchers at Ledger Donjon while examining the Nothing CMF Phone 1. Their work demonstrated that an attacker could bypass the phone’s operating system entirely to pull critical security data from a protected area of the chip. This type of attack highlights a significant risk to user data stored on affected devices, including financial information and personal authentication details.
Initially, the research pointed to a vulnerability within the Trusted Execution Environment (TEE) provided by security firm Trustonic, which operates on the MediaTek chip. The TEE is designed as a secure, isolated zone within a processor to safeguard sensitive operations. Yet, in a detailed rebuttal, Trustonic has pushed back against this characterization. The company asserts its security software, known as Kinibi, functions correctly on other chipset platforms and implies the flaw is inherent to MediaTek’s specific implementation.
“This issue does not exist on other SoC vendor products where we are using the same version of Kinibi,” a Trustonic representative stated. The firm further noted that it was not required to issue a software update because MediaTek had already provided the necessary corrective patches to device manufacturers. According to Trustonic, the fix was distributed on January 5, 2026.
This clarification shifts the focus squarely onto the chipset architecture. If the vulnerability stems from MediaTek’s platform rather than a third-party security layer, it potentially affects every device using those processors, regardless of the brand or specific security software installed. Trustonic emphasized that its technology is not present on all MediaTek devices, suggesting the original report may have incorrectly narrowed the scope of at-risk phones.
MediaTek confirmed it released a security patch in January to address the issue. However, the full extent of impacted devices remains unclear. The patch must be integrated by individual phone makers and delivered to end-users via firmware updates, a process that can be slow and inconsistent across different brands and models. The effectiveness of the fix ultimately depends on manufacturers pushing timely updates and users installing them.
The research team at Ledger Donjon has not yet commented on Trustonic’s statements or provided further details on the vulnerability’s scope. It is also unknown whether the Nothing CMF Phone 1, the device used in the demonstration, utilizes Trustonic’s technology. This lack of confirmation leaves open questions about the precise mechanism of the exploit and the complete list of vulnerable components.
For consumers, the situation underscores the complex, layered nature of mobile security. A device’s safety relies on the integrity of hardware from the chipmaker, the implementation by the phone manufacturer, and the efficacy of any third-party security services. When a flaw is discovered deep within this stack, remediation can be a fragmented and lengthy endeavor. Users are advised to ensure their devices are running the latest available operating system and security updates to mitigate potential risks.
(Source: Android Authority)