Why Cellebrite Cut Off Serbia Over Phone Hacking Tools
▼ Summary
– Cellebrite suspended Serbian police as customers last year after documented allegations its tools were used to hack a journalist and activist’s phone.
– The company has recently dismissed similar allegations of tool abuse by authorities in Kenya and Jordan, declining to commit to investigating them.
– Researchers at The Citizen Lab found digital traces on victims’ phones they link with “high confidence” to Cellebrite’s unlocking tools in both the Kenya and Jordan cases.
– A Cellebrite spokesperson stated the situations are “incomparable” to Serbia and that “high confidence is not direct evidence,” without detailing the differences.
– While Cellebrite claims to disable tools for human rights violations, it did not commit to investigating the Jordan case and did not comment on the Kenya report.
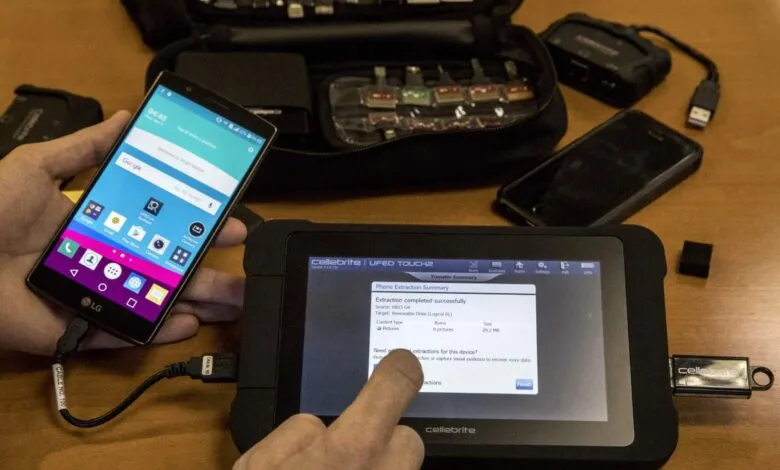
The digital forensics firm Cellebrite made headlines last year by suspending Serbian police from using its phone hacking tools, a direct response to allegations from human rights researchers. The move followed a detailed report from Amnesty International which claimed Serbian authorities had used Cellebrite technology to infiltrate the devices of a journalist and an activist, even planting spyware. This public termination of service stood as a notable instance of the company acting on documented abuse.
However, the company’s recent response to similar, high-profile allegations paints a different picture. Following investigations by the University of Toronto’s Citizen Lab into incidents in Jordan and Kenya, Cellebrite has dismissed the claims and declined to commit to any internal review. This shift in approach raises questions about the consistency of its enforcement policies.
In a report released this week, Citizen Lab researchers alleged that Kenyan authorities used Cellebrite tools to unlock the phone of activist and politician Boniface Mwangi while he was detained. A separate report from January accused the Jordanian government of breaking into the phones of several local activists and protesters using the same technology. In both cases, the conclusions were based on forensic traces of a specific application found on the victims’ devices, an application previously linked to Cellebrite through digital certificates on the VirusTotal malware repository.
Cellebrite spokesperson Victor Cooper defended the company’s position, stating the situations were “incomparable” to the Serbia case and that “high confidence is not direct evidence.” He emphasized that the company does not respond to speculation and urged organizations to share evidence-based concerns directly. When pressed on whether Cellebrite would investigate the latest reports or clarify the differences from the Serbian incident, Cooper did not respond to repeated follow-up inquiries.
For both the Kenya and Jordan investigations, Citizen Lab provided Cellebrite with an opportunity to comment prior to publication. In response to the Jordan allegations, the company issued a general statement that any substantiated misuse would result in immediate disablement of its tools, but it did not commit to investigating that specific case or disclose customer information. Regarding Kenya, Cellebrite merely acknowledged receipt of the inquiry without providing any comment.
Researcher John Scott-Railton, who worked on the investigations, called for greater transparency. “We urge Cellebrite to release the specific criteria they used to approve sales to Kenyan authorities, and disclose how many licenses have been revoked in the past,” he stated. “If Cellebrite is serious about their rigorous vetting, they should have no problem making it public.”
This is not the first time Cellebrite has severed ties following abuse reports. The company, which boasts over 7,000 law enforcement customers globally, previously cut off relationships with Bangladesh, Myanmar, Russia, and Belarus in 2021. It also ceased sales in Hong Kong and China, citing U.S. export regulations, after local activists accused authorities of using its tools to unlock protesters’ phones. The contrast between these past actions and its current stance on Kenya and Jordan highlights an evolving and inconsistent challenge in regulating the use of powerful surveillance technology.
(Source: TechCrunch)