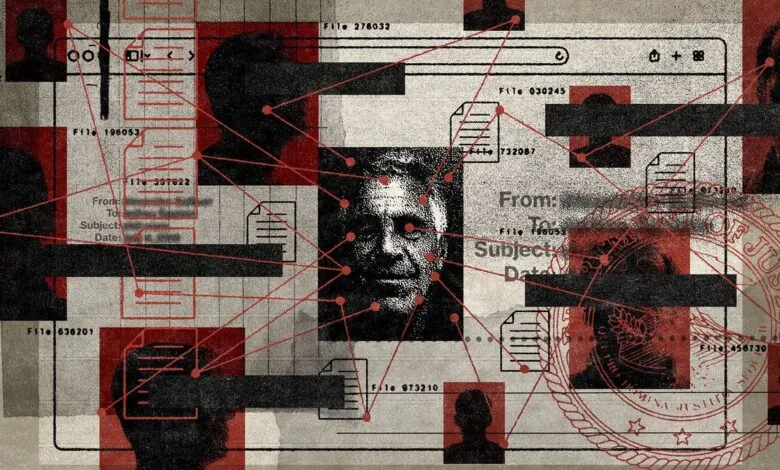
The Man Who Built the Definitive Epstein Database
▼ Summary
– The Justice Department’s Epstein document library was chaotic and disorganized, making it difficult for researchers like Keller to navigate and connect key information fragments.
– Frustrated by manual searching, Keller, a database professional, built a basic search prototype overnight to process the documents more efficiently.
– He was inspired by the community-built tool Jmail.world, which demonstrated that volunteers could create better investigative interfaces than the government provided.
– Keller’s project evolved to focus on cross-referencing and connecting different document types (emails, flights, wire transfers) to map the network of people and events.
– After a major document release, he undertook a meticulous, nightly process of converting, analyzing, and verifying files to systematically reconstruct the evidence.
The sheer volume of documents released in the Jeffrey Epstein case presents a monumental challenge for researchers and journalists, with a disorganized government database making it nearly impossible to connect crucial pieces of evidence. One individual, a database infrastructure professional named Keller, found himself scrolling through the chaotic archive late one night, overwhelmed by the fragmented nature of the material. He realized that tracing a single name across dozens of files was a task perfectly suited for a database, not manual labor. This realization sparked the creation of a powerful, private search tool designed to cross-reference people, flights, financial transactions, and testimonies across the entire document set.
His frustration with the official “Epstein Library” was profound. The files were often poorly scanned, inconsistently redacted, and lacked any coherent structure, turning basic research into a disorienting puzzle. After a four-hour manual search for one person, he opened his code editor and by 3 a.m. had built a basic working prototype. This initial effort coincided with the launch of other community tools, like Jmail.world, which presented Epstein’s emails in a familiar Gmail-style interface. These projects validated his belief that public collaboration could produce far superior investigative resources than those provided by official channels.
Keller’s vision, however, aimed higher than organizing a single document type. He wanted to map the entire network. His goal became creating a system that could link a person mentioned in an email to a flight manifest, then to a wire transfer, and finally to a deposition. Solving this cross-referencing problem was the core technical challenge. When the Justice Department released a massive new tranche of documents in mid-December, his prototype became the essential engine for processing the avalanche of new data, ballooning his nightly workload.
The process was grueling and meticulous. After his day job, he would work into the early morning hours, processing documents that were often posted as non-searchable image files. He ran pages through multiple layers of optical character recognition software to convert them to text, then used specialized systems to extract entities like names, dates, and locations. His workflow included hash verification to ensure file integrity and redaction analysis to spot inconsistencies in government censorship. He tracked every step in a detailed, color-coded digital ledger, approaching the task not as simple file management but as the painstaking reconstruction of a crime scene from millions of evidentiary fragments.
For Keller, the work was deeply personal. The nature of the allegations described in the documents compelled him to continue, driven by an understanding that went beyond mere curiosity. He saw his database not as an endpoint, but as a foundational tool, a meticulously organized index of a sprawling scandal that could help others find the connections he knew were buried within the chaos. His nights of cold coffee and countless open tabs were dedicated to building a clearer map of a very dark network.
(Source: Wired)
