A major resurgence of LummaStealer malware is being driven by sophisticated social engineering campaigns that use a technique called ClickFix…
Read More »Rhadamanthys
Entity category: PRODUCT
Global law enforcement is achieving unprecedented coordination, with major international operations dismantling cybercrime networks and seizing billions in illicit assets…
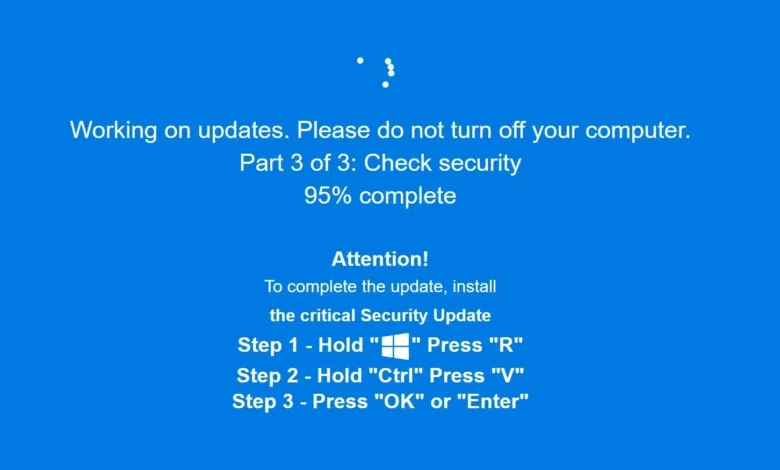
Read More »A deceptive malware campaign uses a fake Windows Update screen to trick users into manually executing malicious commands, leading to…
Read More »A deceptive cyberattack called ClickFix tricks users by mimicking a Windows security update, using a full-screen browser animation to install…
Read More »Ransomware activity surged in Q3 2025, with compromised VPN credentials being the primary entry point for nearly half of all…
Read More »Dutch law enforcement dismantled a major bulletproof hosting service used exclusively by cybercriminals, seizing approximately 250 physical servers and taking…
Read More »Operation Endgame 3.0 dismantled three major malware networks—Rhadamanthys, VenomRAT, and Elysium—through a coordinated international law enforcement effort across eleven countries.…
Read More »The Rhadamanthys infostealer malware service has been disrupted, with criminal subscribers losing access to their data-collection servers, possibly due to…
Read More »TA585 is a sophisticated cybercriminal group known for its fully autonomous infrastructure, managing its own phishing campaigns, malware deployment, and…
Read More »