The Interlock ransomware group exploited a critical zero-day vulnerability (CVE-2026-20131) in Cisco's Secure Firewall Management Center for over a month…
Read More »ClickFix
Entity category: technology
LeakNet ransomware uses a stealthy "bring your own runtime" attack, employing the legitimate Deno software to run malicious code directly…
Read More »Threat actors are now using generative AI to create custom malware, as evidenced by the AI-assisted "Slopoly" backdoor deployed in…
Read More »A sophisticated malware campaign uses fake installation pages, promoted via paid Google ads, to trick developers searching for the Claude…
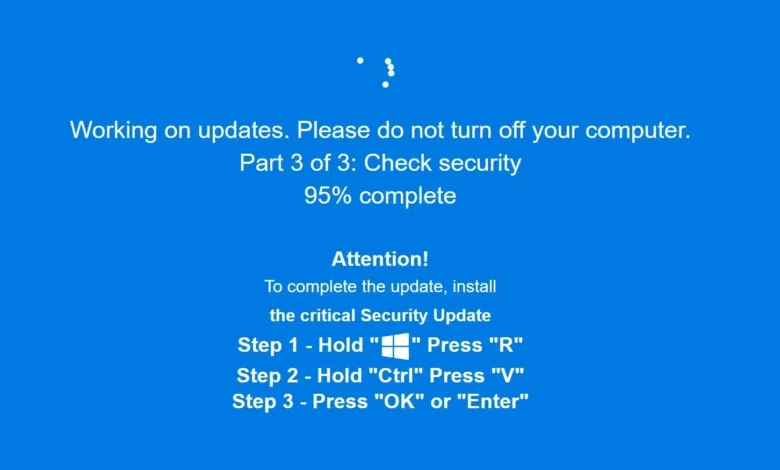
Read More »The Velvet Tempest cybercrime group uses a social engineering technique called ClickFix, tricking users into executing a malicious command that…
Read More »AI is dramatically accelerating cyberattacks, with threat actors using automation to reduce the average breakout time to just 34 minutes,…
Read More »Web browsers are involved in nearly half of all cybersecurity incidents, making them a primary target for varied threats like…
Read More »A major resurgence of LummaStealer malware is being driven by sophisticated social engineering campaigns that use a technique called ClickFix…
Read More »The web browser is now the primary workspace for critical business tasks, yet it remains a major security blind spot,…
Read More »The TA584 threat actor has significantly escalated operations, tripling campaign volume in late 2025 and expanding its geographic targeting to…
Read More »A malicious browser extension named NexShield, fraudulently marketed as an ad blocker, intentionally crashes Chrome and Edge by exhausting system…
Read More »A sophisticated phishing campaign targets the European hospitality industry by impersonating Booking.com, using a fake website and a fabricated Windows…
Read More »A cybercriminal group named Zestix is selling sensitive data stolen from dozens of organizations by exploiting compromised employee credentials on…
Read More »Push Security has launched a malicious copy-and-paste detection feature to disrupt ClickFix-style attacks by blocking the execution of harmful scripts…
Read More »A new phishing campaign called **ConsentFix** compromises Microsoft accounts by exploiting the legitimate Azure CLI OAuth application, bypassing passwords and…
Read More »A new malware campaign called "ClickFix" uses Google Ads impersonating AI platform guides to distribute the AMOS infostealer, tricking users…
Read More »Attackers are exploiting trusted security tools like EDR software and Windows utilities to deploy malware with stealth and persistence, shifting…
Read More »A deceptive cyberattack called "JackFix" tricks users by mimicking adult websites like xHamster and PornHub, hijacking screens with fake Windows…
Read More »A deceptive malware campaign uses a fake Windows Update screen to trick users into manually executing malicious commands, leading to…
Read More »A deceptive cyberattack called ClickFix tricks users by mimicking a Windows security update, using a full-screen browser animation to install…
Read More »