30,000 Facebook Accounts Hacked in Google AppSheet Phishing Scam
▼ Summary
– A Vietnamese-linked operation named AccountDumpling uses Google AppSheet as a phishing relay to steal Facebook accounts, selling them via an illicit storefront.
– The campaign has compromised an estimated 30,000 Facebook accounts, primarily targeting Business account owners with fake Meta Support emails.
– Phishing lures include Netlify-hosted help center pages, Vercel-hosted “Security Check” pages, Google Drive PDFs, and fake job offers from companies like Meta and Apple.
– Stolen data—including credentials, 2FA codes, and government IDs—is exfiltrated to attacker-controlled Telegram channels.
– Metadata from Canva-generated PDFs identifies a Vietnamese name, “PHẠM TÀI TÂN,” linking the operation to a digital marketing services website.
A sophisticated phishing campaign linked to Vietnamese threat actors has compromised an estimated 30,000 Facebook accounts by exploiting Google AppSheet as a delivery mechanism. Security researchers at Guardio have tracked this operation under the codename AccountDumpling, revealing a complete criminal ecosystem where stolen accounts are resold through an illicit storefront.
“This wasn’t a single phishing kit,” explained security researcher Shaked Chen in a report shared with The Hacker News. “It was a living operation with real-time operator panels, advanced evasion, continuous evolution and a criminal-commercial loop that quietly feeds on the same accounts it helps steal back.”
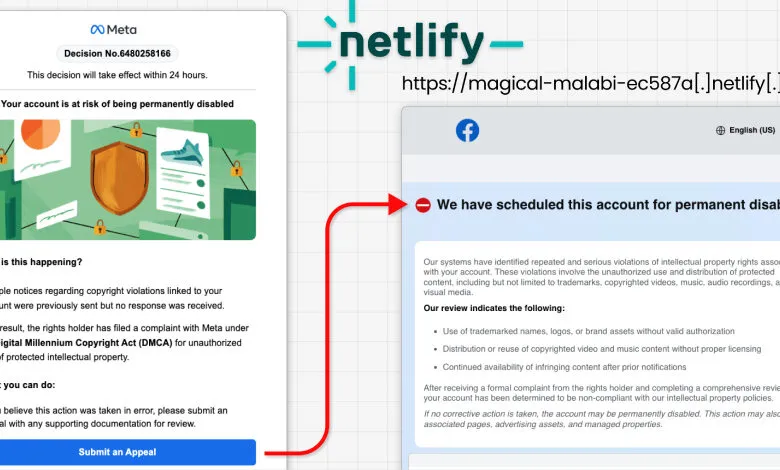
The campaign represents the latest evolution in Vietnamese threat actors’ tactics to gain unauthorized access to Facebook Business accounts for profit on underground markets. The attack chain begins with a phishing email targeting Facebook Business account owners, impersonating Meta Support and warning of permanent account deletion unless the recipient submits an appeal. Crucially, these emails originate from a legitimate Google AppSheet address (“noreply@appsheet.com”), allowing them to bypass standard spam filters.
This manufactured urgency drives victims to a fake credential-harvesting page. A similar campaign was documented by KnowBe4 in May 2025.
Over recent weeks, the attackers have diversified their lures to create what Chen describes as “Meta-related panic.” The four primary clusters identified include Netlify-hosted fake Facebook help center pages that steal credentials, dates of birth, phone numbers, and government-issued ID photos, all forwarded to an attacker-controlled Telegram channel. Another cluster uses Vercel-hosted “Security Check” or “Meta | Privacy Center” pages gated by a fake CAPTCHA, then collects contact details, business information, credentials, and two-factor authentication (2FA) codes after forcing a retry. A third cluster distributes Google Drive-hosted PDFs generated from a free Canva account, masquerading as account verification instructions to harvest passwords, 2FA codes, government ID photos, and browser screenshots via html2canvas. The fourth uses fake job offers impersonating companies like WhatsApp, Meta, Adobe, Pinterest, Apple, and Coca-Cola to build rapport and direct victims to attacker-controlled sites.
Across the first three clusters, Telegram channels contain approximately 30,000 victim records, primarily from the U. S., Italy, Canada, the Philippines, India, Spain, Australia, the U. K., Brazil, and Mexico. Most victims have been locked out of their accounts.
The operation’s origin became clear through metadata in the PDFs, which listed a Vietnamese name “PHẠM TÀI TÂN” as the author. Open-source intelligence led to a website (“phamtaitan[.]vn”) offering digital marketing services. A February 2023 post on X from that handle stated it “specializes in providing digital marketing services, marketing resources, and consulting on effective digital marketing strategies.”
“Taken together, they form a consistent picture of a large, Vietnamese-based, mega operation,” Chen concluded. “This campaign is bigger than a single AppSheet abuse. It’s a window into the dark market around stolen Facebook assets, where access, business identity, ad reputation, and even account recovery have all become tradable commodities. Another entry in the pattern we keep surfacing: trusted platforms repurposed as delivery, hosting, and monetization layers.”
(Source: Internet)