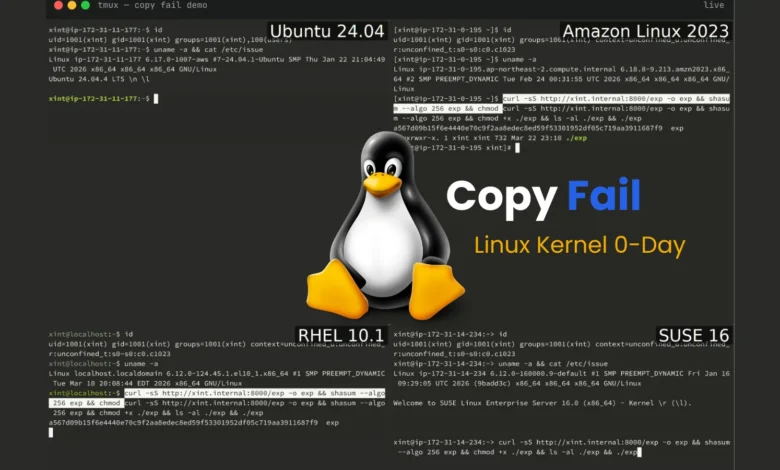
A critical Linux kernel zero-day vulnerability (CVE-2026-31431, "Copy Fail") allows any unprivileged local user to gain root access on nearly…
Read More »Cybersecurity
Keep up with cybersecurity threats, data privacy, hacking incidents, and digital protection strategies. Learn about security tools, expert insights, and best practices to safeguard your online presence.
Instructure, the company behind the Canvas learning management system, confirmed a cybersecurity incident by a criminal threat actor and is…
Read More »New Mexico is seeking a court order in a public nuisance trial to impose sweeping changes on Meta, including mandatory…
Read More »AI tools have intensified the global cyber insecurity crisis by empowering attackers with unprecedented speed and sophistication, enabling automated reconnaissance,…
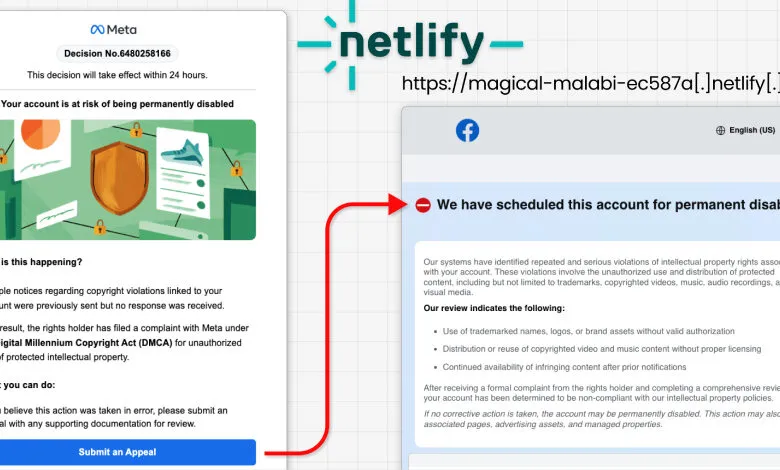
Read More »A Vietnamese-linked phishing campaign called "AccountDumpling" compromised roughly 30,000 Facebook accounts by using legitimate Google AppSheet emails to bypass spam…
Read More »Anthropic has launched Claude Security in public beta for Enterprise customers, using Claude Opus 4.7 to scan codebases and identify/patch…
Read More »Two U.S. cybersecurity professionals, Ryan Goldberg and Kevin Martin, were each sentenced to four years in federal prison for facilitating…
Read More »A critical Linux kernel vulnerability called Copy Fail (CVE-2026-31431) affects nearly all distributions since 2017, allowing any user to escalate…
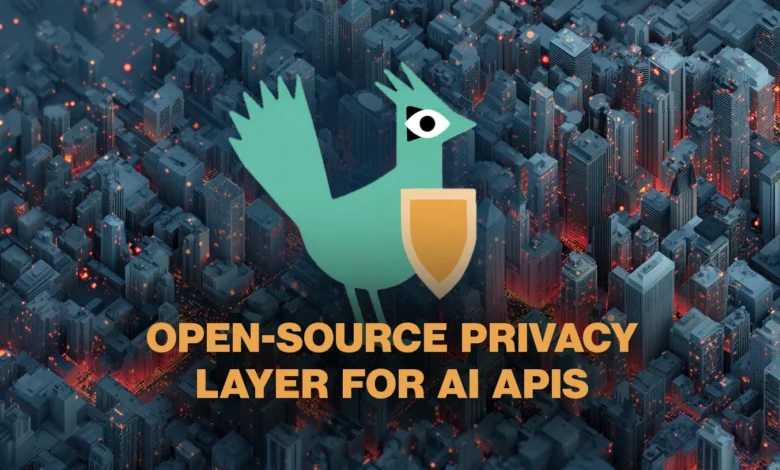
Read More »Dataiku's Kiji Privacy Proxy is an open-source local gateway that detects and masks personally identifiable information (PII) in prompts sent…
Read More »Between one-fifth and one-third of workers use AI outside IT governance, creating a divide between employees with managed AI tools…
Read More »Mallory launched an AI-native threat intelligence platform that monitors thousands of threat sources and contextualizes data against a user's actual…
Read More »A critical Linux privilege escalation vulnerability, CVE-2026-31431 (CopyFail), has been publicly exploited, allowing attackers to gain root access on virtually…
Read More »Minnesota has become the first U.S. state to pass a law specifically targeting AI nudification apps, with unanimous legislative approval…
Read More »Bluekit is a new phishing-as-a-service platform offering over 40 ready-made templates for major services (email, cloud, crypto) and an AI…
Read More »Amazon Web Services confirmed full recovery from Iranian drone strikes on its UAE and Bahrain data centers will take several…
Read More »Anthropic launched Claude Security, a defensive cybersecurity tool in public beta for Enterprise users, that scans codebases for vulnerabilities and…
Read More »AI-driven cyberattacks can weaponize software vulnerabilities in under an hour for less than a dollar, compressing attack timelines from months…
Read More »A new cross-government guide from CISA and federal partners titled "Adapting Zero Trust Principles to Operational Technology" provides actionable steps…
Read More »The Marsh 2026 People Risks report identifies cyber-threat literacy as the top risk, with tech skills shortages and AI adoption…
Read More »A critical authentication-bypass vulnerability (CVE-2026-41940) in cPanel and WebHost Manager (WHM) allows attackers to remotely seize full control over affected…
Read More »