The traditional security model of relying solely on identity verification is inadequate for today's distributed workforce, as it fails to…
Read More »zero trust security
Imprivata has expanded its Enterprise Access Management platform to eliminate passwords, aiming to provide faster, more secure access by consolidating…
Read More »The NSA has released new Zero Trust Implementation Guidelines (ZIGs) to provide a flexible, phased path for organizations to achieve…
Read More »The NSA has released a phased implementation guide for Zero Trust security, translating principles into actionable tasks to help organizations…
Read More »Businesses are rapidly adopting AI, but this creates new security vulnerabilities as traditional cybersecurity tools fail to protect AI systems'…
Read More »The NSA has released new Zero Trust Implementation Guidelines, starting with a Primer and Discovery Phase, to provide a structured,…
Read More »The cybersecurity landscape is defined by a dangerous synergy between AI and human ingenuity, creating adaptive, automated threats that require…
Read More »AppGate has introduced Agentic AI Core Protection to extend zero-trust security principles directly to AI workloads, enabling secure innovation across…
Read More »The Firewalla Orange is a portable, pocket-sized device that functions as a high-performance Wi-Fi 7 router and multi-gigabit firewall, bringing…
Read More »Zero trust security shifts from assuming internal network trust to continuously verifying every user, device, and application attempting to access…
Read More »Businesses are rapidly adopting AI assistants to boost productivity, but this introduces new security vulnerabilities that traditional models cannot handle,…
Read More »Quantum computing threatens modern encryption systems like RSA and Elliptic Curve cryptography, which secure online communications, digital signatures, and cryptocurrency…
Read More »Zscaler's ZDX platform now offers enhanced performance monitoring that reduces issue detection time by 98% and resolution times from days…
Read More »The autonomy of AI agents introduces security vulnerabilities in Zero Trust architectures by bypassing continuous verification requirements through inherited or…
Read More »Businesses in Australia and Oceania are facing a sharp rise in sophisticated cyberattacks, and adopting a Zero Trust security architecture…
Read More »Netskope's Universal ZTNA platform now integrates Private Access and Device Intelligence, offering deeper threat inspection and enabling businesses to replace…
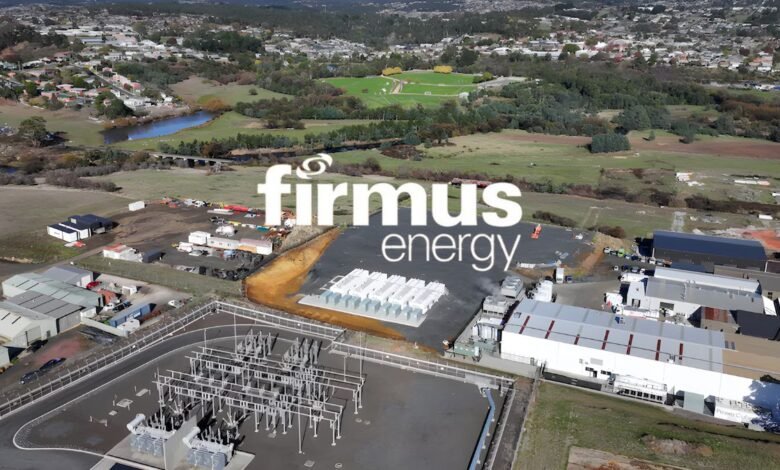
Read More »Tasmania's "Green AI Factory" project by Firmus has drawn scrutiny for its contradictory branding and reliance on substantial public funding,…
Read More »Cybersecurity Awareness Month emphasizes the need for collective digital defense as identity-based attacks, accounting for nearly 80% of incidents, exploit…
Read More »FireCloud Total Access unifies four security protections into a single cloud-managed platform, offering enterprise-level Zero Trust security accessible to managed…
Read More »Zero trust is a continuous process, not a one-time project, requiring ongoing adaptation due to evolving threats, changing technology, and…
Read More »