All Related Articles for: Hacker "Patches" Own Vulnerability to Lock Out Rivals
Found 18 articles related to this post based on shared entities and topics.
-
 February 15, 202612%
February 15, 202612%Brutus: Open-Source Offensive Security Tool for Credential Testing
Brutus is an open-source, multi-protocol credential testing tool written…
Entity similarity: 20% | Topic similarity: 0%Read More » -
 January 1, 202612%
January 1, 202612%Duplicati: Free Open-Source Backup Software
Duplicati is a free, cross-platform backup tool that creates…
Entity similarity: 20% | Topic similarity: 0%Read More » -
 March 29, 202612%
March 29, 202612%Malware hidden in backdoored Telnyx PyPI package
A malicious version of the Telnyx SDK Python package…
Entity similarity: 20% | Topic similarity: 0%Read More » -
 March 22, 202612%
March 22, 202612%32-Year-Old Bug in GNU Telnetd Enables Pre-Auth RCE (CVE-2026-32746)
A critical 32-year-old buffer overflow vulnerability (CVE-2026-32746) in the…
Entity similarity: 20% | Topic similarity: 0%Read More » -
 September 16, 202512%
September 16, 202512%Hackers Now Use RMM Tools for Phishing Attacks
Threat actors are using legitimate remote monitoring and management…
Entity similarity: 20% | Topic similarity: 0%Read More » -
 January 10, 202612%
January 10, 202612%China-Linked Hackers Breach Telcos via Edge Devices
A China-linked cyber espionage group, UAT-7290, has expanded from…
Entity similarity: 20% | Topic similarity: 0%Read More » -
 November 18, 202512%
November 18, 202512%Kraken Ransomware Evolves With Advanced Benchmarking
In August 2025, the Kraken ransomware group emerged as…
Entity similarity: 20% | Topic similarity: 0%Read More » -
 March 4, 202612%
March 4, 202612%Cloudflare Blocks 230 Billion Daily Threats: Key Findings
Modern cyber threats are massive and automated, with over…
Entity similarity: 19% | Topic similarity: 0%Read More » -
 January 19, 202612%
January 19, 202612%Startup Battlefield 200: The 2026 Roadmap Revealed
The TechCrunch Startup Battlefield 200 is a highly selective…
Entity similarity: 19% | Topic similarity: 0%Read More » -
 February 17, 202611%
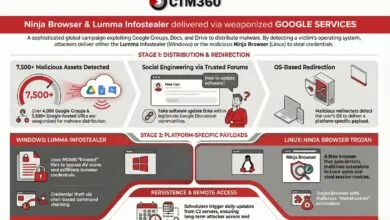
February 17, 202611%Lumma Stealer & Ninja Malware Hijack Google Groups
A widespread malware campaign exploits Google's trusted services, using…
Entity similarity: 10% | Topic similarity: 13%Read More » -
 February 12, 202611%
February 12, 202611%Hackers Use SolarWinds Flaws to Deploy DFIR Tool in Attacks
Cybersecurity researchers have identified an active campaign exploiting critical…
Entity similarity: 10% | Topic similarity: 13%Read More » -
 February 11, 202611%
February 11, 202611%Active Attacks Target Unpatched SolarWinds WHD Systems
Attackers are exploiting unpatched SolarWinds Web Help Desk systems…
Entity similarity: 10% | Topic similarity: 13%Read More » -
 December 4, 202511%
December 4, 202511%Noisy Ransomware Uncovered a Long-Term Espionage Operation
A ransomware group's disruptive attack on two Russian companies…
Entity similarity: 10% | Topic similarity: 12%Read More » -
 August 24, 202511%
August 24, 202511%APT36 Hackers Use Linux .desktop Files to Deploy Malware in Latest Campaign
A cyber espionage campaign by Pakistani-linked group APT36 is…
Entity similarity: 10% | Topic similarity: 12%Read More » -
 January 7, 202611%
January 7, 202611%VVS Stealer Malware Hijacks Discord Accounts Using Python
A new, affordable Python-based malware called **VVS Stealer** is…
Entity similarity: 9% | Topic similarity: 12%Read More » -
 June 9, 202510%
June 9, 202510%Last Chance: Apply for Startup Battlefield 200 Today!
The application deadline for Startup Battlefield 200 at TechCrunch…
Entity similarity: 17% | Topic similarity: 0%Read More » -
 July 25, 202510%
July 25, 202510%7 Money-Saving Benefits of Using Linux
Linux is free to use, eliminating costly operating system…
Entity similarity: 17% | Topic similarity: 0%Read More » -
 September 19, 202510%
September 19, 202510%Ransomware Hackers Exploit Misconfigured EDR to Disable Security
Modern ransomware groups exploit minor security oversights, such as…
Entity similarity: 10% | Topic similarity: 11%Read More »