All Related Articles for: Unlock LLM Responses: Psychological Tricks for "Forbidden" Prompts
Found 32 articles related to this post based on shared entities and topics.
-
 September 7, 202554%
September 7, 202554%How to Make AI Break Its Own Rules
A University of Pennsylvania study found that psychological persuasion…
Entity similarity: 76% | Topic similarity: 21%Read More » -
 August 4, 202527%
August 4, 202527%Can Sergey Brin’s Threat Prompts Boost AI Accuracy? Study Reveals
A study explored whether unconventional prompts like threats or…
Entity similarity: 45% | Topic similarity: 0%Read More » -
 April 4, 202618%
April 4, 202618%AI Users Surrender Logic, Study Reveals
A new study identifies "cognitive surrender," where people outsource…
Entity similarity: 26% | Topic similarity: 6%Read More » -
 December 25, 202516%
December 25, 202516%Baker University Data Breach Exposes 53,000 People in 2025
A data breach at Baker University compromised the sensitive…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 December 3, 202516%
December 3, 202516%University of Pennsylvania Discloses New Data Breach Following Oracle Hack
The University of Pennsylvania suffered a data breach after…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 February 14, 202615%
February 14, 202615%Figure Data Breach Exposes Fintech Lending Giant
Figure Technology suffered a data breach due to a…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 January 28, 202615%
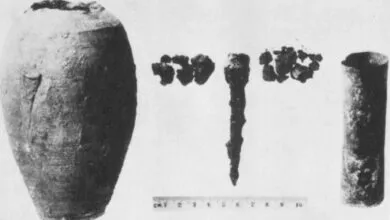
January 28, 202615%Ancient Battery? Scientists Probe 2,000-Year-Old Artifact
The Baghdad battery is a controversial artifact from Iraq,…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 January 25, 202615%
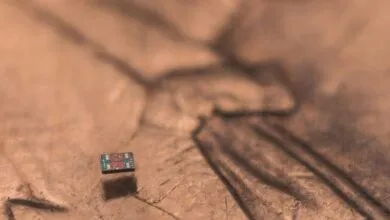
January 25, 202615%World’s Smallest Autonomous Aquatic Robot
Researchers have created a fully autonomous robot smaller than…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 November 18, 202515%
November 18, 202515%Princeton University Data Breach Exposes Donor, Alumni Info
A sophisticated phishing attack on a Princeton University employee…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 November 7, 202515%
November 7, 202515%University of Pennsylvania Data Stolen in Cyberattack
The University of Pennsylvania experienced a cybersecurity breach where…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 November 4, 202515%
November 4, 202515%Penn Data Breach: 1.2 Million Donor Records Stolen by Hacker
A data breach at the University of Pennsylvania exposed…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 November 1, 202515%
November 1, 202515%University of Pennsylvania Data Breach Exposed in Hack
The University of Pennsylvania experienced a cybersecurity incident where…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 October 29, 202515%
October 29, 202515%Teens Dive Into Tech at IEEE TryEngineering Summer Camp
The IEEE TryEngineering Summer Institute is a nine-day residential…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 September 27, 202515%
September 27, 202515%Who’s Waging War on Science?
The 21st century is increasingly defined by severe environmental…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 September 1, 202515%
September 1, 202515%Chatbots Vulnerable to Flattery and Peer Pressure
AI chatbots, despite ethical safeguards, are vulnerable to psychological…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 February 27, 202615%
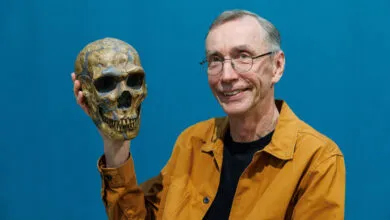
February 27, 202615%Neanderthals May Have Preferred Mating With Early Modern Humans
Research reveals a mutual bias: Neanderthal X chromosomes also…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 February 21, 202615%
February 21, 202615%MIT Study: AI Agents Are Fast, Loose, and Out of Control
A major study of 30 agentic AI systems reveals…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 February 18, 202615%
February 18, 202615%AI-Powered Defense Agents: The Future of Military Tech
Advanced AI is being integrated to directly control military…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 February 18, 202615%
February 18, 202615%AI-Powered Hunt for Antibiotics in Unexpected Places
AI is revolutionizing antibiotic discovery by analyzing vast genetic…
Entity similarity: 26% | Topic similarity: 0%Read More » -
 January 21, 202615%
January 21, 202615%Macaques Use Facial Expressions to Communicate, Study Shows
Research aims to decode the neural basis of facial…
Entity similarity: 26% | Topic similarity: 0%Read More »