All Related Articles for: Ransomware Strikes Most After Hours
Found 34 articles related to this post based on shared entities and topics.
-
 February 20, 202615%
February 20, 202615%Telegram Channels Reveal SmarterMail Exploits in the Wild
Threat actors are rapidly weaponizing critical vulnerabilities in SmarterMail…
Entity similarity: 25% | Topic similarity: 0%Read More » -
 January 25, 202615%
January 25, 202615%Hybrid Work Drives Surge in Active Directory Password Resets
The shift to hybrid work has drastically increased costly…
Entity similarity: 25% | Topic similarity: 0%Read More » -
 January 7, 202615%
January 7, 202615%Generative AI Supercharges Active Directory Attacks
Generative AI is making sophisticated password attacks cheaper, faster,…
Entity similarity: 25% | Topic similarity: 0%Read More » -
 December 4, 202515%
December 4, 202515%Secure Active Directory with UserLock IAM: Product Showcase
UserLock is a modern IAM layer for Microsoft Active…
Entity similarity: 25% | Topic similarity: 0%Read More » -
 November 1, 202515%
November 1, 202515%The Critical Role of Password Security in Cybersecurity
Password security remains critical despite advanced threats, with stolen…
Entity similarity: 25% | Topic similarity: 0%Read More » -
 March 10, 202615%
March 10, 202615%Hackers Exploit Flaws, Use Elastic Cloud to Manage Stolen Data
Attackers exploited software vulnerabilities to steal system data and…
Entity similarity: 25% | Topic similarity: 0%Read More » -
 April 10, 202615%
April 10, 202615%$30,000 GPU Password Cracking Test: Results
A benchmark test found that high-end consumer GPUs, like…
Entity similarity: 25% | Topic similarity: 0%Read More » -
 February 21, 202615%
February 21, 202615%From Stolen Credentials to Fake Identities: How Infostealers Operate
Modern infostealer malware harvests vast, detailed data dumps that…
Entity similarity: 25% | Topic similarity: 0%Read More » -
 December 2, 202515%
December 2, 202515%Why Ransomware Attacks Spike on Weekends
Threat actors deliberately target organizations on weekends and holidays…
Entity similarity: 25% | Topic similarity: 0%Read More » -
 March 26, 202615%
March 26, 202615%BAS vs. Automated Pentesting: Why You Need Both
The article argues that Breach and Attack Simulation (BAS)…
Entity similarity: 24% | Topic similarity: 0%Read More » -
 November 28, 202515%
November 28, 202515%Code Beautifiers Leak Bank, Government, and Tech Credentials
A security lapse in JSONFormatter and CodeBeautify exposed thousands…
Entity similarity: 24% | Topic similarity: 0%Read More » -
 November 27, 202515%
November 27, 202515%Code Formatting Sites Leak User Secrets and Credentials
Popular online code formatting platforms like JSONFormatter and CodeBeautify…
Entity similarity: 24% | Topic similarity: 0%Read More » -
 March 28, 202614%
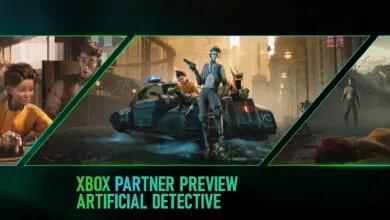
March 28, 202614%Artificial Detective: Xbox Gameplay Breakdown and Details
The game "Artificial Detective" is set in a vast,…
Entity similarity: 23% | Topic similarity: 0%Read More » -
 January 9, 202611%
January 9, 202611%Top 6 Cyber Threats to Watch in 2026
The cybersecurity landscape is defined by a dangerous synergy…
Entity similarity: 0% | Topic similarity: 26%Read More »