The majority of successful breaches stem from fundamental failures in identity management, third-party access controls, and perimeter device security, with…
Read More »SOC
Entity category: organization
The global cybersecurity job market is robust, with high demand for specialized roles in areas like cloud security, penetration testing,…
Read More »Cloud adoption has introduced new security vulnerabilities, such as dynamic infrastructure and multi-cloud architectures, creating blind spots that require network…
Read More »SECNAP has launched CloudJacket MXDR, a next-generation managed cybersecurity platform that integrates network detection and response (NDR) with other security…
Read More »The global cybersecurity field offers diverse, high-demand career paths ranging from strategic leadership roles like Chief Information Security Officer (CISO)…
Read More »Darktrace has enhanced its EMAIL platform to better detect sophisticated multi-channel attacks and prevent data loss, using its core Self-Learning…
Read More »Security leaders face a rapidly growing vulnerability backlog due to fragmented tools and slow remediation, with the mean time to…
Read More »Security analysts must creatively piece together limited digital evidence from various sources to reconstruct cyberattacks, as investigations are often complicated…
Read More »Veeam Software has launched the Veeam App for Microsoft Sentinel to enhance data resilience and operational efficiency by integrating backup…
Read More »Trellix has integrated Hyperautomation into its Helix platform, featuring a no-code, drag-and-drop workflow builder to automate security processes and boost…
Read More »Corelight's new Flow Monitoring solution for AWS provides unified network visibility across cloud and hybrid infrastructures, reducing SIEM and storage…
Read More »AI significantly improves the speed and accuracy of security investigations, helping analysts combat fatigue and burnout in high-pressure environments. AI-supported…
Read More »Exabeam has been recognized as a Leader in the Gartner Magic Quadrant for SIEM for the sixth consecutive year, underscoring…
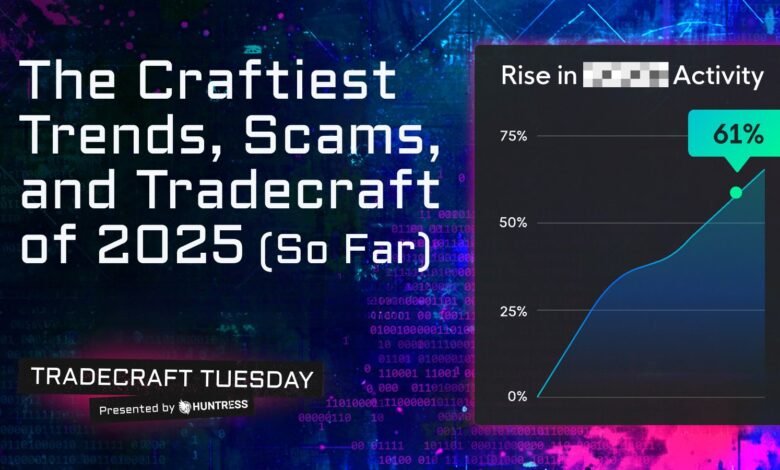
Read More »Business email compromise (BEC) attacks use psychological manipulation rather than technical exploits, bypassing traditional security by mimicking trusted communications and…
Read More »Realm.Security secured $15 million in Series A funding, led by Jump Capital, bringing its total funding to $20 million to…
Read More »Cancer Council Queensland has partnered with Macquarie Telecom to enhance its IT infrastructure, enabling the charity to focus more resources…
Read More »A new ransomware called "Obscura," discovered in late August 2025, uses domain infrastructure to stealthily spread across corporate networks by…
Read More »GreyNoise Intelligence has launched an MCP Server to integrate real-time threat intelligence into AI-driven security operations, enabling faster decision-making and…
Read More »Security operations centers are overwhelmed by excessive data and false alerts, which often obscure critical threats. ManageEngine's Log360 update introduces…
Read More »EASM tools are critical for identifying and managing external vulnerabilities by discovering internet-facing assets and exposures that attackers could target.…
Read More »