A Russian-speaking hacker exploited exposed management interfaces and weak credentials to breach over 600 Fortinet firewalls across 55 nations, using…
Read More »Go
Entity category: technology
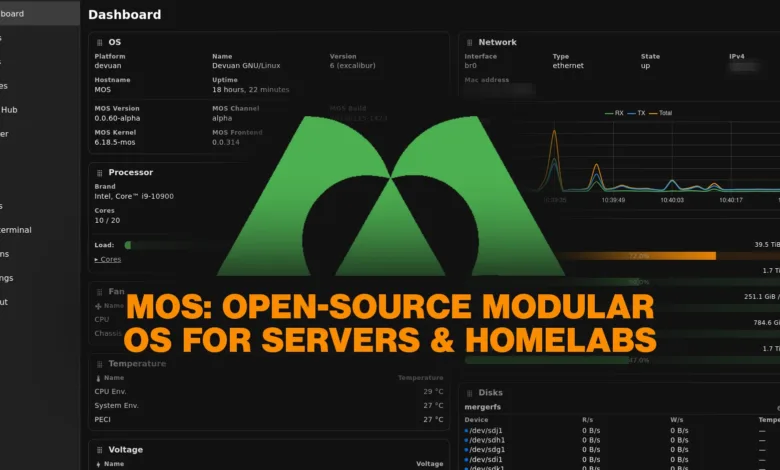
MOS is a new open-source operating system built on Devuan, offering a unified web interface and API to streamline server…
Read More »Brutus is an open-source, multi-protocol credential testing tool written in Go, designed as a single binary to streamline workflows and…
Read More »OpenAI is introducing high-priced ads to ChatGPT, charging about $60 per 1,000 impressions, which is roughly triple the industry standard.…
Read More »OpenAI will introduce non-intrusive, clearly marked advertisements to ChatGPT's free and lower-tier plans, ensuring ads do not influence the chatbot's…
Read More »A critical remote code execution flaw (CVE-2025-8110) in Gogs is being actively exploited, allowing attackers to run arbitrary commands by…
Read More »Rob Pike, a prominent software engineer, publicly condemned an unsolicited AI-generated thank-you email, criticizing the immense resource cost of such…
Read More »A sophisticated malware campaign named FlexibleFerret targets macOS systems using a multi-stage attack to bypass security, deploy a persistent backdoor,…
Read More »The Nobel Prize in Chemistry doesn't usually go to computer scientists. But Demis Hassabis, the mind behind Google DeepMind, just…
Read More »Google has identified new AI-driven malware families like PromptFlux and PromptSteal that use large language models to dynamically generate malicious…
Read More »OpenFGA is an open source authorization engine inspired by Google's Zanzibar, enabling fine-grained, relationship-based access control for applications of any…
Read More »TA585 is a sophisticated cybercriminal group known for its fully autonomous infrastructure, managing its own phishing campaigns, malware deployment, and…
Read More »Rollercoaster Tycoon was uniquely programmed entirely in assembly language by Chris Sawyer, allowing for precise control and high performance, which…
Read More »A new ransomware called "Obscura," discovered in late August 2025, uses domain infrastructure to stealthily spread across corporate networks by…
Read More »A new botnet called ShadowV2 uses cloud tools like GitHub CodeSpaces and Docker to deploy malware that launches powerful DDoS…
Read More »A cyberattack campaign called FileFix uses steganography to hide malicious code in JPG images, delivered via a phishing site that…
Read More »Slovakia-based cyber security vendor ESET said it has discovered "the first known" artificial intelligence-powered ransomware that generates malicious scripts on-the-fly…
Read More »A cyber espionage campaign by Pakistani-linked group APT36 is targeting Indian government and defense sectors using malicious Linux .desktop files…
Read More »Google has launched Mangle, an open-source programming language built on Datalog to simplify deductive database programming and handle fragmented data…
Read More »Government cybersecurity agencies recommend memory-safe languages (e.g., Rust, Swift, Go) to reduce vulnerabilities like buffer overflows and use-after-free flaws. Transitioning…
Read More »