Small and medium-sized businesses are significantly increasing cybersecurity budgets due to mounting digital threats and the adoption of AI, moving…
Read More »Cybersecurity
Keep up with cybersecurity threats, data privacy, hacking incidents, and digital protection strategies. Learn about security tools, expert insights, and best practices to safeguard your online presence.
A Reddit user reported that the metal contacts on the Steam Controller's charging puck caused a fire hazard by short-circuiting…
Read More »Threat actors exploited incomplete patches for CVE-2024-12802 on SonicWall Gen6 SSL-VPN appliances to bypass multi-factor authentication, using brute-forced credentials to…
Read More »A security flaw in WordPress 7.0 exposes AI API keys via the browser's autofill feature, displaying them as plain text…
Read More »Palantir held a spring hack week to address employee unease over its DHS and ICE contracts by developing new oversight…
Read More »AI-accelerated scams using social engineering tactics have become the fastest growing source of consumer harm, with fraudsters manipulating victims into…
Read More »Identity verification alone is no longer sufficient for security, as AI-powered phishing, credential theft, and session hijacking allow attackers to…
Read More »On 4chan's /r/ board, anonymous users request and create deepfake nude images of women from publicly available photos, with skilled…
Read More »GitHub confirmed a security breach after TeamPCP infiltrated its internal repositories via a compromised VS Code extension installed by an…
Read More »A cybercriminal group called TeamPCP has transformed software supply chain attacks into an almost weekly occurrence, poisoning hundreds of open…
Read More »Since early 2026, researchers have tracked approximately 2.8 million attacks from the CypherLoc scareware strain, which locks browsers and directs…
Read More »Vulnerability exploitation has overtaken compromised credentials as the most common initial breach vector for the first time in nearly 20…
Read More »Discord has enabled end-to-end encryption for all voice and video calls by default, ensuring that no one, including Discord itself,…
Read More »A GitHub employee's device was compromised after installing a malicious VS Code extension, leading to approximately 3,800 internal repositories being…
Read More »Microsoft is developing a patch for CVE-2026-45585 ("YellowKey"), a BitLocker bypass vulnerability requiring physical access that affects Windows 11 and…
Read More »Cybersecurity investment has been skewed toward technical controls while undervaluing people, processes, and organizational dynamics, leading to a focus on…
Read More »CVE Lite CLI, now an OWASP Incubator Project, shifts dependency vulnerability scanning from late-stage CI pipelines to the developer's terminal,…
Read More »A new Columbia Law School study found that nine popular employee monitoring tools ("bossware") all shared sensitive user data, including…
Read More »Microsoft's 2019 acquisition of GitHub for $7.5 billion was met with mixed reactions, but nearly eight years later, the platform…
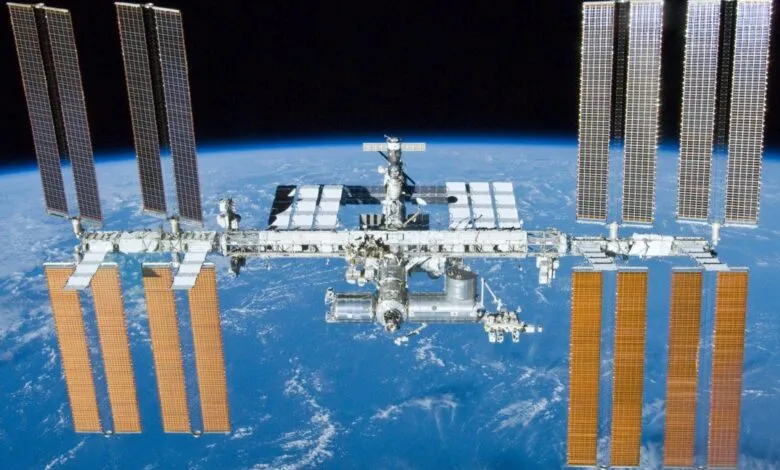
Read More »The Russian segment of the International Space Station has resumed leaking air into space due to microscopic structural cracks, a…
Read More »