Google is embedding its Gemini generative AI across its ecosystem, raising significant privacy concerns due to the vast user data…
Read More »Cybersecurity
Keep up with cybersecurity threats, data privacy, hacking incidents, and digital protection strategies. Learn about security tools, expert insights, and best practices to safeguard your online presence.
Denuvo's DRM technology has been fully cracked by hackers using a hypervisor-based bypass (HVB), rendering it ineffective for offline PC…
Read More »A cybercrime forum post analyzed by Flare outlines a structured OPSEC framework for high-volume carding, focusing on long-term operational security…
Read More »GitHub patched a critical remote code execution vulnerability in its internal git infrastructure within six hours, which could have allowed…
Read More »Checkmarx suffered a supply-chain attack on March 19 via compromised Trivy GitHub accounts, and then its own GitHub account was…
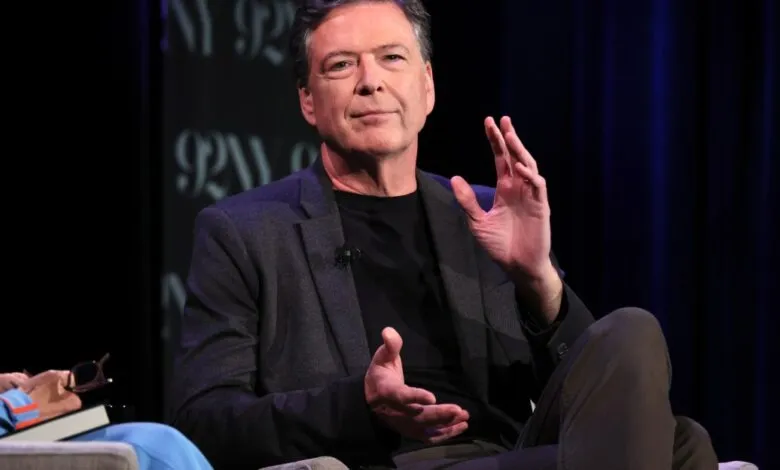
Read More »The DOJ has indicted former FBI Director James Comey for allegedly threatening President Trump via a now-deleted Instagram post featuring…
Read More »Attackers exploited a flaw in Robinhood's account creation process to inject malicious HTML into legitimate emails from noreply@robinhood.com, which passed…
Read More »The GlassWorm campaign has deployed 73 sleeper extensions on the OpenVSX ecosystem, with only 6 activated so far delivering malware,…
Read More »The UAE's cybercrime laws, particularly Article 52, impose severe penalties for spreading false news or misinformation online, with minimum sentences…
Read More »A proposed Colorado bill, SB26-090, that would have weakened the state's 2024 right-to-repair law by creating a vaguely defined "critical…
Read More »The FIDO Alliance, with contributions from Google and Mastercard, is launching two working groups to develop industry standards for securing…
Read More »ADT suffered a data breach by the ShinyHunters group, exposing personal data of 5.5 million individuals including names, phone numbers,…
Read More »On Thursday, April 30 at 2:00 PM ET, BleepingComputer is hosting a live webinar with Flare and threat intelligence researcher…
Read More »Itron confirmed a cybersecurity breach in an SEC filing, where an unauthorized third party accessed its internal IT systems, prompting…
Read More »A critical 15-year-old vulnerability in OpenSSH was discovered, originating from a code reuse bug where commas in certificate principals were…
Read More »Google reports a rise in malicious AI prompt injection attacks, but notes their overall sophistication remains low, with many indirect…
Read More »Three quarters of cybersecurity professionals believe they are not paid fairly, and half are actively seeking new jobs, according to…
Read More »A new cyber extortion group, CL-CRI-1116, linked to BlackFile and "The Com," has targeted retail and hospitality sectors since February…
Read More »The Supreme Court case "Chatrie v. United States" challenges the legality of geofence warrants, which law enforcement used to track…
Read More »Red Hat principal software engineer Sally O'Malley unveiled Tank OS, an open source tool using Podman containers to deploy and…
Read More »